In a recent study that Google researchers carried out with colleagues from the University of California at Berkeley, they discovered that more than a third of Chrome extensions that injected ads were classified as malware. This translated into 192 deceptive Chrome extensions that affected 14 million users. Google has received more than 100,000 complaints from Chrome users since the beginning of 2015, relating to network errors, performance problems, or some other issue.
Unwanted Chrome ad injector extensions: Bad for users, advertisers, publishers
In Chrome, any extension hosted in the Chrome Web Store must comply with the Developer Program Policies. These require that extensions have a narrow and easy-to-understand purpose. We don’t ban injectors altogether—if they want to, people can still choose to install injectors that clearly disclose what they do—but injectors that sneak ads into a user’s browser would certainly violate our policies, said Google.
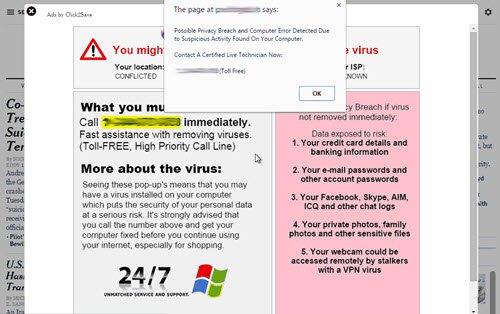
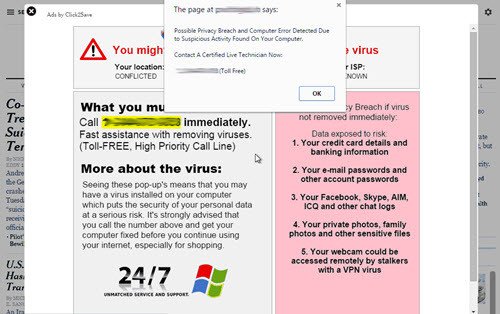
Ad injectors are unwanted programs that inject new ads into the pages you browse. These programs are deceptive, difficult to remove and secretly tied with other downloads. They waste advertisers’ money and spoil the browsing experience.
In such cases, advertisers are not aware that their ads are being injected, which means they have no information where their ads are running. Publishers do not get compensated and unknowingly put their visitors to risk of spam and malware.
The study further discovered widespread use of ad injectors for multiple browsers on both Windows and OS X computers. More than 5% of Google Chrome users have at least one ad injector installed. Of that 5%, half have at least two injectors installed, and nearly one-third have at least four installed.
This crackdown comes less than two month after Lenovo sold computers that came preinstalled with adware from a company called Superfish. Not only did this software inject ads, it also hijacked encrypted web sessions and made users vulnerable to attacks that could completely bypass HTTPS protections.