Win32/Virlock is a new type of ransomware that not only locks the screen, but it also behaves as a polymorphic parasitic virus that infects files on the user’s machine. So, we have a new virus having a combination of a ransomware that locks user’s screen, a polymorphic malware and a parasitic virus that infects user’s files as well. With these characteristics, Win32/Virlock poses a greater threat to users than any other, typical ransomware.
Win32/Virlock ransomware
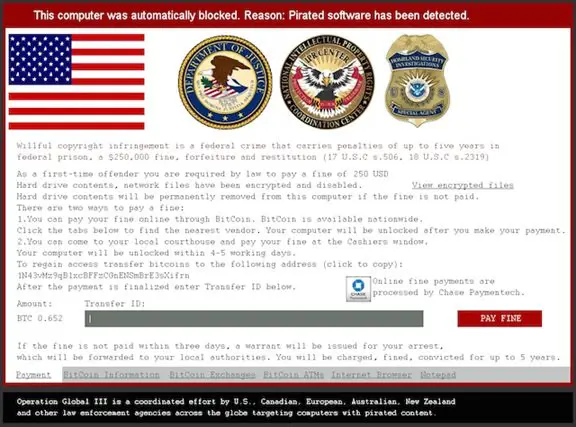
A typical ransomware screen looks as follows:
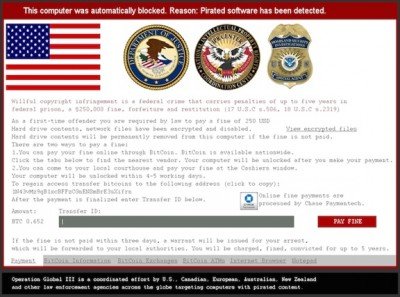
In general, a ransomware will often stop you from using your computer. They claim that you done something illegal and you are fined for that. Or the ransomware will lock your screen ad demand for money to give away the key to unlock it. The methods are one of these or a combination of all.
There are generally two types of ransomware defined, namely LockScreen and Filecoder. Their characteristics are as follows:
- LockScreen Ransomware: The ransomware locks user’s screen and then demands for ransom to unlock it.
- Filecoder Ransomware: The ransomware does not lock user’s screen or prevents the user from using the computer. However, it encrypts the files on his PC and asks for fees to decrypt the files.
ESET mentions their first experience with Win32/Virlock as follows:
“In October we discovered a new, previously unseen approach – Win32/VirLock is ransomware that locks the screen and then not only encrypts existing files, but also infects them by prepending its body to executable files – thus acting as a parasitic virus.”
In the overview of Win32/Virlock, ESET mentions how this ransomware is different than the typical file coders,
“A file infected with VirLock will be embedded into a Win32 PE file and the .exe extension appended to its name unless it was already an executable file. When it is executed, it decrypts the original file from within its body, drops it to the current directory and opens it. The decryption methods are described later in the article. This behavior clearly sets it apart from typical file coders.”
Though the virus seems pretty harmful, ESET’s analysis show that the number of victims is relatively low. It is also not widespread like other ransomware. ESET mentioned that they are keeping an eye on this new breed of ransomware and will keep updating the information about it.
You can read more about Win32/Virlock ransomware at the ESET blog.
Check out our post on general steps to take to stay protected & prevent Ransomware.