According to the latest Microsoft Security Intelligence Report, Pakistan, Indonesia, the Palestinian territories, Bangladesh, and Nepal are some of the Asian countries, where the highest number of malware attacks is reported. Microsoft’s team uploaded this report on its ‘Microsoft Security Intelligence Report’ website.
The authors of this SIR report mention that it focuses on software vulnerabilities, software vulnerability exploits, malware, and unwanted software. This particular SIR report is named as “PLATINUM: Targeted attacks in South and Southeast Asia”, which can be downloaded from the website.
In this report, Microsoft mentioned that the team constantly monitors the threat landscape for emerging threats. Part of this job involves keeping tabs on targeted activity groups, which are often the first ones to introduce new exploits and techniques that are later used widely by other attackers. PLATINUM is the code name of a newly discovered targeted activity group and the report is published to raise the awareness of the group’s activities.
The report also mentions,
“PLATINUM has been targeting its victims since at least as early as 2009, and may have been active for several years prior. Its activities are distinctly different not only from those typically seen in untargeted attacks, but from many targeted attacks as well.”
As per the data in this report, some countries like Japan, Sweden, Finland and Norway have faced fewer attack. This data was gathered using the sensors in the systems running Microsoft anti-malware software.
Microsoft’s manager Alex Weinert mentions in his statements,
“We look at north of 10 million attacks on identities every day,”
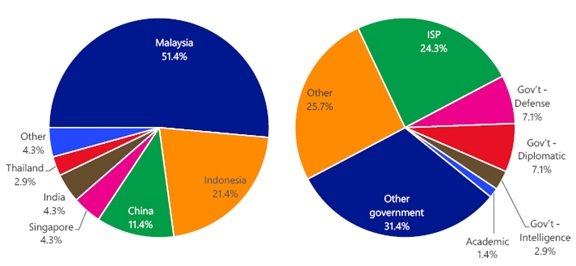
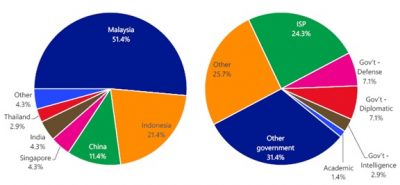
However, not all the attacks succeed in their objective. According to the Microsoft Security Intelligence Report nearly half of all malware attacks have originated in Asia and nearly one-fifth of the attacks originated in Latin America. These attacks take place when the attacker has valid credentials, such as user name and password.
You can download this and previous SIR reports from the SIR website.