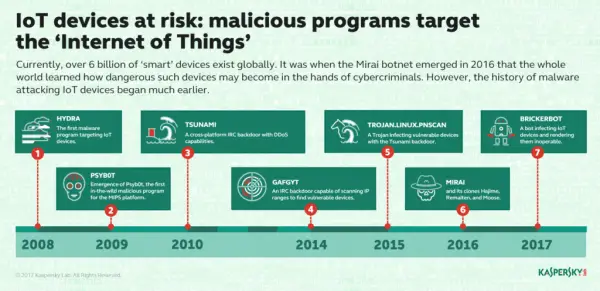
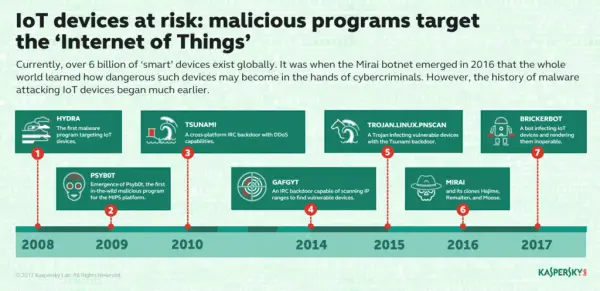
Kaspersky recently conducted an experiment where it highlighted inherent risks associated with the large-scale integration of digital devices with our physical world. it suggested that integrating more and more devices with the Internet makes the susceptible to trojans and malware attacks. These attacks not just harm vulnerable devices but also render them inoperable.
The attacks mainly exploit vulnerabilities in software used for the manufacture of such devices. Also, little or practically no experience in dealing with cyber security, make manufacturers incapable of controlling the damage during any such breakouts.
Botnets, mainly made up of routers, IP cameras, printers and other devices triggered these attacks. For instance, PNScan infects devices with the Tsunami backdoor while Persirai Trojan relies on IP cameras. Preset passwords used by the manufacturer too, help in the spread of attacks. In some cases, it affects manufacturer’s entire product range.
IOT devices & Honeypots
Kaspersky Lab ran an experiment in which it set up several Honeypots (traps) imitating as various devices running Linux, and left them connected to the Internet to see what happened to them ‘in the wild’. In just a few seconds time there were multiple attempts to the open telnet port. The number rose to tens of thousands in 24 hours. In most cases, the attempted connections used the telnet protocol; the rest used SSH.
When analyzing the activities of IoT botnets, Kaspersky discovered something important. It found that the infection was region specific i.e., confined to few pockets like China, Vietnam, Russia and developing countries like Brazil in South America. Also, there were certain days of the week which recorded sharp surges in malicious activity.
The main problems of smart devices is with the Firmware, Passwords, telnet and SSH. The security research giant made some recommendations to help you safeguard your devices from the infection like, not allowing access to your device from outside of your local network, unless you specifically need it to use your device and disabling all network services that you don’t need to use your device.
You can find the complete list of recommendations on Kaspersky Labs website page.