Microsoft has been lately working a lot on the security front and as a result has come out with additional security layers including Credential Guard, Enterprise Data Protection, Device Guard, Antimalware Scan Interface, Windows Hello, etc. On the other hand, Windows Defender has been fighting malware and other attacks on nearly 300-Million devices every day. Microsoft has now announced a few more steps in making the Internet a safer place, especially for its enterprise customers.
Sharp Increase in the Cyber Attacks
With the increase in the total number of people on the Internet it is but obvious that the number of Cybercriminals is also on rise. Attackers are holding on to social engineering and zero-day vulnerabilities in order to gate-crash the corporate networks. According to a recent research it apparently takes an enterprise more than 200 days in order to detect and additional 80 days to fix the same.
These attacks are not just incredibly expensive in nature but they also hinder the productivity of the entire organisation. That being said, the attacks are also presuming a deadlier form and this calls for the need of Enterprise level security solutions.
Improvised Windows Defender Advanced Threat Protection
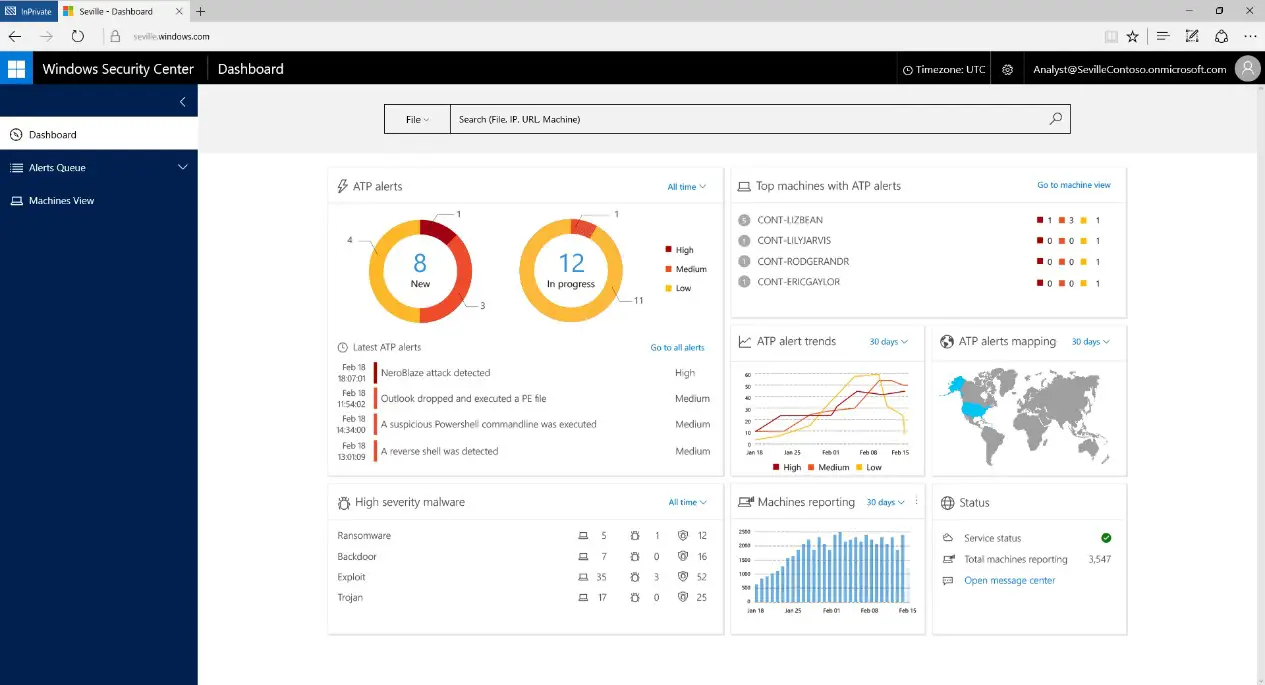
The program detects advanced attack and it will take cue from the world’s largest array of sensors and expert advanced threat protection which will also include the team of security experts from Microsoft in certain case.
The core of the Windows Defender Advanced Threat Protection is a blend of Windows behavioral sensors, cloud based security analytics, threat intelligence and assistance from the Microsoft intelligent security graph.
The security graph is the very premise on which the program identifies any anomalies and this graph has indexed anonymous information from more than 1 billion Windows devices, 2.5 trillion indexed URL’s and also more than 1 million suspicious files flagged off daily, says the blog post. Microsoft has also expanded the scope of Windows Defender ATP. It also helps defend against Ransomware infections in Corporate Networks.
Security operations data shapes up as an effortless way to investigate the entire network for signs of invasion and then obtain the detailed footprints from the concerned organization. In order to facilitate comprehensive check-up the Threat Protection examines the state of machines and their activities in the recent past.
You can read more about this at Microsoft.