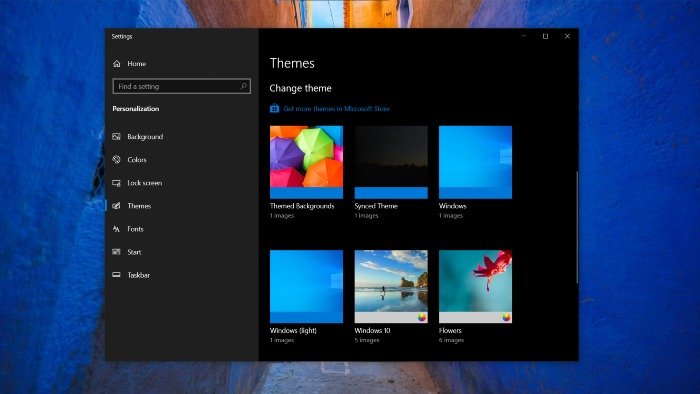
Who doesn’t like to customize the default look and feel of their Windows 10 operating system? Windows 10 users can personalize their computers with a wide variety of custom themes. But something they probably don’t know yet is that a new sort of attack may be taking shape.
Windows 10 themes attack could be on the rise
Security researchers believe attackers can exploit Windows 10 themes to steal Windows account credentials, courtesy of ‘Pass-the-hash’ attack. Let’s first understand what this attack is all about.
Before we can understand the pass-the-hash attack, we need to understand what the hash is. When a user logs onto a Windows PC and enters a username and password, the password is never sent over the network. Instead, a hash is derived from the password.
Interestingly, a password hash can uniquely represent the actual plain-text password that can’t be mathematically reversed. It also can’t reveal what the password is. This hash is known as the NTLM hash.
Windows account credentials and NTLM hash are stored in memory that’s managed by a process called Local Security Authority (LSASS.exe), which allows for single sign-on. Hence, when the user needs to access other resources on the network.
In the pass-the-hash attack, attackers can authenticate to a remote server or service by using the underlying NTLM hash of a Windows 10 user’s password for authentication and potentially Lateral Movement technique to control RDP servers.
Coming back to attackers potentially abusing Windows 10 themes, a security researcher (@bophos) has revealed how custom themes can help threat actors steal Windows passwords.
[Credential Harvesting Trick] Using a Windows .theme file, the Wallpaper key can be configured to point to a remote auth-required http/s resource. When a user activates the theme file (e.g. opened from a link/attachment), a Windows cred prompt is displayed to the user 1/4 pic.twitter.com/rgR3a9KP6Q
— bohops (@bohops) September 5, 2020
Well, Pass-the-Hash attacks are successful when attackers trick their victims into accessing a WebDAV or SMB location requiring authentication. In a Windows .theme file, the wallpaper key can be configured to point to a remote auth-required HTTP/HTTPS resource.
“The default handler loads rundll32.exe (themecpl.dll) and the Themes setting dialogue. I discovered this a while back, and reported it to MSRC earlier this year when I saw that similar “disclosure” bugs were patched. This was not patched b/c this is a “feature by design”
“From a defensive perspective, block/re-associate/hunt for “theme”, “themepack”, “desktopthemepackfile” extensions. In browsers, users should be presented with a check before opening. Other CVE vulns have been disclosed in recent years, so it is worth addressing and mitigating”
When a user activates the theme file, a Windows credential prompt is displayed to the user. The wallpaper key is located under the “Control Panel\Desktop” section of the .theme file. This technique can help attackers disclose NTLM hash when the key is set to a remote location.
You must set up multi-factor authentication on your Microsoft accounts. Hence, even if the attacker has managed to steal your Windows credentials, your Microsoft account can’t be remotely accessed.
