CryptoLocker has become a reason for rising panic among the Microsoft Windows-based computers users for the last few weeks. A malware variant that fits in the ‘ransomware’ category primarily spreads through email attachments where it arrives as an executable file disguised as a PDF file, packed into a zip attachment. If opened, the malware encrypts the user’s documents across local hard drives of an infected computer.
CryptoLocker Ransomware
Once the malware takes over you system, the owner receives a ransom demand, payable within 72 hours. Unfortunately, the victim has no option but to pay up to regain access to the encrypted files. Antivirus programs attempting to remove the infection from compromised machines remove the registry key that is essential to pay the ransom and decrypt the files. That then leaves the victim in the lurch.
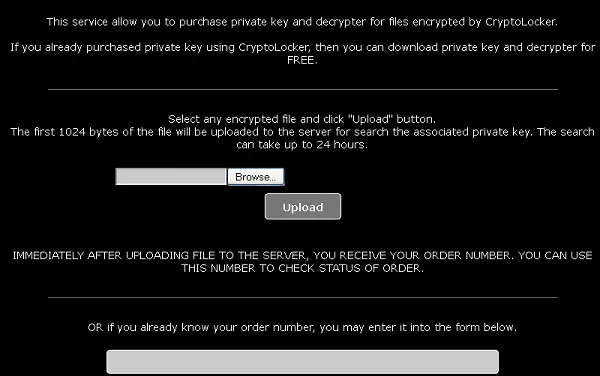
Payment is allowed via either an anonymous pre-paid cash voucher or Bitcoin. Victim has to upload one of their encrypted files to find the corresponding private decryption key. If a match is found, a confirmation page is displayed, along with the demand for payment of Bitcoins.
Earlier, the malware authors offered victims 3 days deadline to make the payment but now they have extended the deadline, giving victims a second chance to recover their files, but at a much higher cost. CryptoLocker manages to avoid detection by investigators looking to identify it by following the money trail somehow.
That said, it is easier and cheaper to block CryptoLocker than to remove it once it has affected the computer. Simply exercise some precautionary steps before hitting the ‘OPEN’ button for unknown email attachments. Also, make sure you have your PC up-to-date and if an anti-virus or anti-malware program is installed, it supports real-time detection.
Lastly, always keep a backup of your important data with you. Cloud Backups, with automatic sync disabled, is a good idea too, suggests Malwarebytes.
This post on how to prevent Ransomware will suggest steps to take to stay protected and offer links to ransomware removal tools.
Leave a Reply