There is a new Ransomware for you to deal with and it requires more attention than before. The new threat, known by the name of “Fantom Ransomware” disguises itself as a legitimate Microsoft Windows Update to trick users click malicious links to infect their PC.
It is known fact and recommended by security experts to update operating systems and software in order to keep away from online threats. However, Fantom Ransomware exploits this very idea of updates and thus can be very difficult to detect.
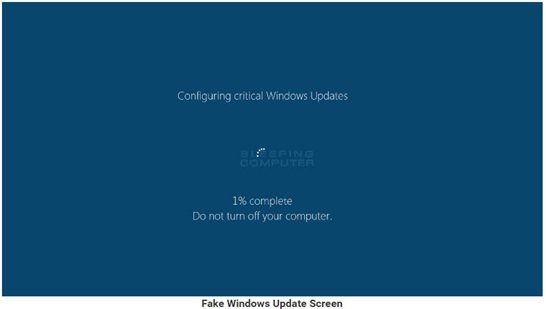
Fantom is based on the open-source EDA2 ransomware project and secretly encrypts victim’s files while mimicking a Windows Update. Currently, there is no way to currently decrypt Fantom. Even the usual methods for getting EDA2 based ransomware keys are not available with this variant.
Fantom is more likely to affect Enterprise users because it mimics an update screen that most business users will recognize as legitimate, perhaps, as a usual update from the IT admins. Hence chances of enterprise users suspecting about the update remain very low.
Fantom ransomware masquerades as Windows Update
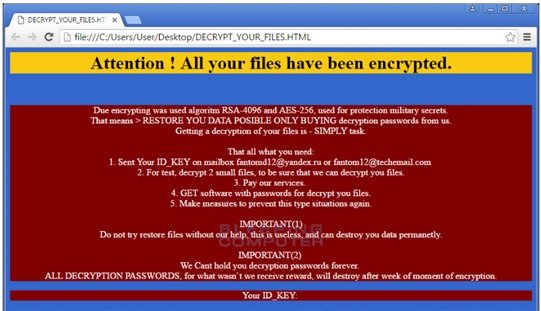
Fantom Ransomware generates an AES-128 key and encrypts it using familiar RSA. The malware after that uploads it to the developers Command & Control server. Fantom then scans the local drives to encrypt the files adding .fantom extensions to them.
As mentioned on BleepingComputer,
“Fantom will also create two batch files that are executed when the encryption is finished. These batch files will delete the shadow volume copies and fake Windows update executable”.
Once the encryption is completed, Fantom displays the ransom note called DECRYPT_YOUR_FILES.HTML that includes the victim’s ID key and asks the victim to send an email to [email protected] or [email protected] so as to receive payment instructions.
However, here is a bit of good news, Fantom Ransomware isn’t really very well-written, nor it has spread on a big scale yet. Hence, there is a big likelihood that you may well escape from falling into its trap.
Stay safe – there are some precautions you can take to prevent ransomware.
