The SaaS model has been picking up the pace and is considered as one of the best platforms to conduct businesses, however, on the other hand, this has also given rise to a large number of malware writers and cyber crooks who are attempting to exploit this model for their own purpose. Ransomware as a service is more like a real world extortion wherein the attacker takes hijacks your system and will release it only once you pay the ransom. Ransom32 is a new kid on the block – and what makes it different is that it is the first JavaScript ransomware!
Ransom32 ransomware
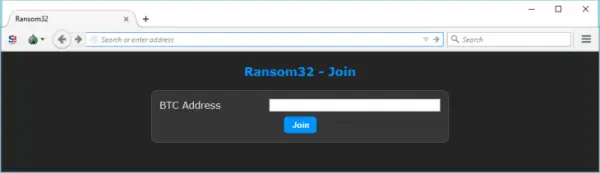
The signup to the ransomware is handled via a hidden server on the Tor network and it will require a Bitcoin address where the funds generated by the ransomware is to be sent. Now that’s not all, Ransom32 also has a full-fledged dashboard for attackers to check out the stats of their Ransomware and if people have paid out. The dashboard will also let you change the amount of Bitcoin, the malware will ask for and will also let the attackers show fake message boxes during installation of the malware.
How it works
Ransom32 is very different from other malware as it will come in the form of a 22MB large malware file as opposed to the other malware files which are usually lesser than 1 MB in size. The malware file, in essence, seems to be a WinRAR self-extracting archive and uses the script language implemented in WinRAR to automatically unpack and dump the content its user’s temporary file directory and thus eventually execute the “Chrome.exe” file in the archive.
The clever part of the malware is the “Chrome.exe” file which looks like the copy of the Chrome browser and the fact that it doesn’t feature a proper digital signature and version information are the tell-tale sign that the file is not the actual Chrome browser and a closer look will tell us that the file has been packaged by NW.js application.
NW.js is actually a framework that facilitates developing of normal desktop applications for Windows, Linux and MacOS X by making use of JavaScript. Nw.js allows for increased degree of control over the operating system allowing it to do anything that a usual run of the mill programming language does.
Ransome32 can be packaged for both Linux and Mac OS X using the NW.js and being a legitimate framework and application, it will not get detected easily.
Read the full details on the Emsisoft blog.
