In collaboration with New York University’s Tandon School of Engineering, Google investigated the perils of Pay-Per-Installs leading to unwanted software installation. Coming out with a report after a year of study on unwanted software distribution, Google found that the Pay-Per-Install affiliate networks support and distribute unwanted software ranging from ad injectors, browser settings hijackers, and system utilities.
Every week Google generates over 60 million warnings related to unwanted software delivered via PPI, three times that of malware, says the report. However, even after the warnings, Chrome Cleanup Tool has found tens of millions of unwanted installs on the user systems. Out of the top 15 families installed, 14 were found to be distributed using commercial PPI.
How Pay-Per-Install works
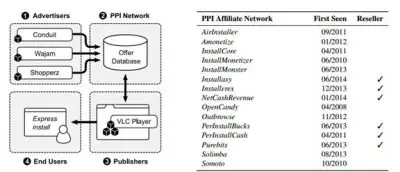
Researchers at Google and the NYU Tandon School of Engineering conducted a year-long study, running a deep research on how software makers are willing to buy installations. Further, how affiliate networks connect software makers with developers of popular apps who are willing to package their software for a fee. And finally, the last culprit, i.e the website publishers who deliver links to the software bundles. All these are the different stakeholders who combine to run the Pay-Per-Install network.
Affiliates play a huge role as they are the ones who forge the deals without user’s consent and package additional software with popular applications and place download offers on well-trafficked websites. These Affiliates are paid by PPI businesses directly starting from as low as $0.10. Although legitimates software makers at times don’t even know that their products are being bundled with extra stuff.
What happens next is a planned forgery at user’s end. With third-party applications already bundled with the legitimate ones, users unknowingly install the whole package containing additional programs as well. Soon there is a bank of ads overrunning the screen continuously asking users to click, install or purchase to overcome a problem or improve the PC. Also, the system’s default browser may be hijacked so as to redirect to ad-laden pages.
Sadly, antivirus programs were also found to be the trafficked that use pay-per-install. AVG Toolbar, LavaSoft ad-aware, Comodo GeekBuddy, and Qihoo 360 were the brands named in the report.
Shockingly, popular names like Opera, Skype, Yahoo Toolbar, and AOL Toolbar were also found to be using pay-per-install as per the report.
Click here to read the PDF report in detail.
