The Android Security team from Google recently released nogotofail, a network traffic security testing tool which test TLS/SSL connection, as being on HTTPS everywhere or HTTPS secured connection is not enough to make program, applications or the World Wide Web safe.
Google Nogotofail
There are many applications designed and developed that use the https secured channel – but this is not considered enough these days after the recent Heartbleed bug which was disclosed this year in the OpenSSL cryptography library. After the Heartbleed bug, the security team at Google has started to develop more secure programs.
As applications are getting more complex, more services that use third party libraries override the default design protocol and this is when the problem starts.
Nogotofail tool helps security researchers and developers detect and fix weak TLS/SSL connections and sensitive cleartext traffic on devices and applications in a flexible and powerful way. Nogotofail includes common SSL certificate, HTTPS and TLS/SSL library bugs, SSL and STARTTTL stripping issues, cleartext issues etc.
The tool depends on Python 2.7 and pyOpenSSL 0.13 and later, and works for iOS, Android, Windows, Linux, Chrome OS, OS X or any device used to connect to the Internet. The tool includes easy-to-use client to configure the settings and get notifications on Android, Linux or attack engine itself deployed on router, proxy server or VPN.
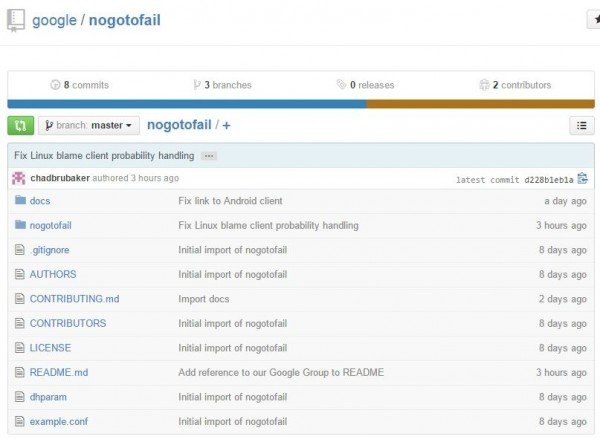
It is available as open source project. The Android security team has worked with different developer to improve the security of their apps and hence to secure the internet, application or tools. Team is looking for support from end user, contributor to help improve the program.
One can find open source project file for nogotofail in the Google repository here.
Whether the Nogotofail tool is really going to take over HTTPS everywhere or any other secured Transport Layer Security (TLS) remains to be seen.
Leave a Reply