With security methods improving by the day, you wouldn’t have expected this but if Rob Fuller, security engineer, is to be believed, there is now a method to snatch your PC login credentials within 30 seconds.
Fuller, who goes by his hacker name ‘mubix‘, in a blog post recently stated one of the simplest bugs that can easily hack into your computer’s login details and access them within a matter of seconds.
The hack works by plugging in a flash-sized computer into an unattended PC that’s logged in but currently locked. In about 30 seconds, the USB drive will obtain the username and password hash used to log into the computer.
The obtained authentication hash can then be cracked to another hash which helps gain easy unauthorized access. If the target machine is running Windows XP and older, the recurring NTLMv1 hash can be converted to NTLM format no matter how complex your plaintext password is.
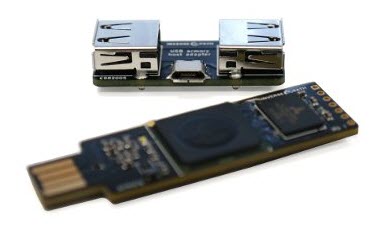
He also mentions that he tried the hack with a $150 USB Armory but claims that even the $50 Hak5 Turtle can work the exact same way. Mubix goes on to describe the basics of his experiment and even states the pros and cons of using alternative tools to hack into the login credentials.
Both the devices he uses – the Hak5 and USB Armory – are fully compliant Linux machines that can emulate an Ethernet device on your computer. Mubix disguised them as a DHCP server in order to gain such a kind of access to the target PCs.
If the $50 Hak5 seems like a cheap device to hack into such sophisticated software, think again. Mubix claims that some people have gotten a similar setup to work on a Raspberry Pi Zero, making the cost of this hack less than $5 but with around 10 minutes of configuration setup.
This video shows how Rob Fuller managed to do the above. He is reportedly working on another project to counter this development of his, due to large concerns about the outcome.