A security researcher from the Eindhoven University of Technology has found a series of vulnerabilities in Intel’s design. Once exploited, these vulnerabilities could allow hackers to gain unauthorized access to old computers. The attack dubbed Thunderspy targets a Thunderbolt port, which is a hardware interface designed by Intel. Thunderbolt port enables the connection between external peripherals and a computer.
Thunderspy attack targets old PC
Björn Ruytenberg, a security researcher warns that all the computers manufactured prior to the year 2019 could be vulnerable to the Thunderspy attack.
In the Thunderspy attack, once an attacker gains brief physical access to a computer with a Thunderbolt port, they can easily read and copy all the private data stored on the computer even though the data is stored on an encrypted hard drive. Plus, it doesn’t matter if the PC is locked or set to sleep.
Thunderspy attackers don’t leave any traces behind, courtesy of stealth attack method.
In his research, Ruytenberg explains:
“Thunderspy is stealth, meaning that you cannot find any traces of the attack. It does not require your involvement, i.e., there is no phishing link or malicious piece of hardware that the attacker tricks you into using.”
Thunderbolt attack: How does it work?
Thunderspy attack occurs even when some of the best security practices are followed such as making use of Secure Boot, strong BIOS and operating system account passwords, full disk encryption, etc.
“All the attacker needs is 5 minutes alone with the computer, a screwdriver, and some easily portable hardware.”
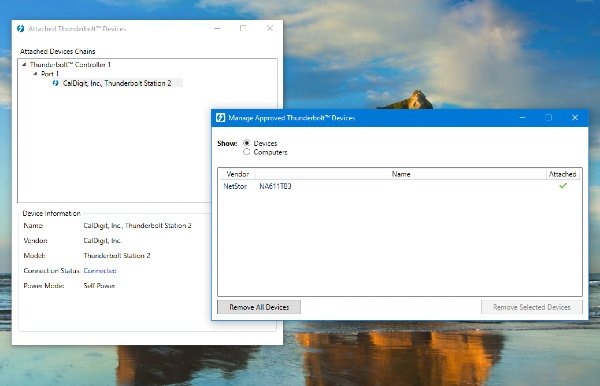
In the Thunderspy attacks, attackers clon user-authorized device identities to their own attacker devices and permanently disabling Thunderbolt security and future firmware updates.
Ruytenberg has revealed a series of vulnerabilities, as follows:
- Inadequate firmware verification schemes
- Weak device authentication scheme
- Use of unauthenticated device metadata
- Downgrade attack using backwards compatibility
- Use of unauthenticated controller configurations
- SPI flash interface deficiencies
- No Thunderbolt security on Boot Camp
Ruytenberg says all Thunderbolt-equipped systems shipped between 2011-2020 are vulnerable to this attack. Unfortunately, these vulnerabilities can only be fixed by a silicon redesign.
Check if your PC is vulnerable to the Thunderspy attack
If you are using a pre-2019 computer running Windows or a Linux OS, you need to check if your machine is vulnerable to the Thunderspy vulnerability.
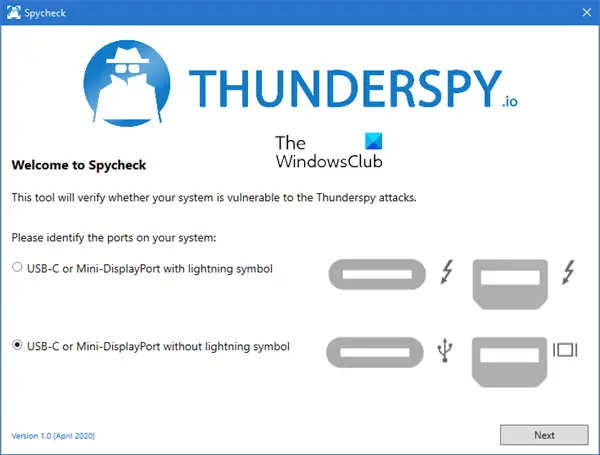
Spycheck tool will users determine whether they are affected by Thunderspy. If your computer is affected, Spycheck will provide users with information on how to help protect their system by updating a driver.
To check if your PC is vulnerable to the Thunderspy attack, download and run the Spycheck tool from thunderspy.io.
Here are some tips to protect your Windows computer against the Thunderspy attack.
