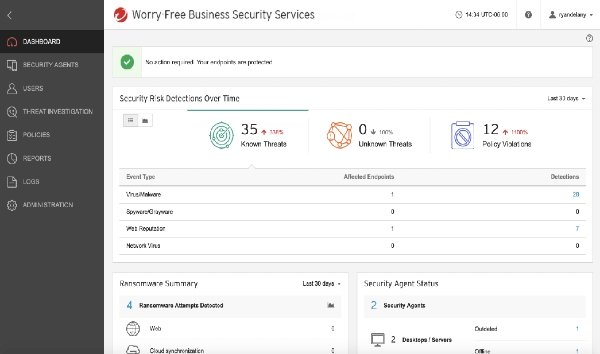
Cybersecurity firm Trend Micro has disclosed a critical directory traversal vulnerability in one of its products. A high-risk vulnerability in Trend Micro Worry-Free Business Security could allow attackers to manipulate a key file to bypass authentication and gain SYSTEM privileges to the management server using Remote Code Execution (RCE). The vulnerability affected Trend Micro Worry-Free Business Security version 9.0, 9.5, and 10.0 for Windows.
Trend Micro vulnerability could bypass server authentication
Researchers at Zero Day Initiative have released an advisory detailing the vulnerability CVE-2020-8600. An attacker could exploit the flaw in order to bypass server authentication, courtesy of improper validation of a user-supplied path prior to using it in file operations.
“This vulnerability allows remote attackers to bypass authentication on affected installations of Trend Micro Worry-Free Business Security. Authentication is not required to exploit this vulnerability.”
“The specific flaw exists within the handling of the TempFileName parameter provided to the cgiRecvFile.exe endpoint.”
Trend Micro says it did not observe any attempted exploits of this vulnerability. According to the company, attackers require physical or remote access to a vulnerable machine to exploit this vulnerability. Meanwhile, Trend Micro has released a patch, recommending affected users to install it as soon as possible.
Aa directory traversal attack (also known as a dot-dot-slash attack) is an HTTP exploit. In this attack, cybercriminals gain access to restricted files and directories outside the web server’s root directory. The basic idea here is to manipulate a URL in such a way that the website will make the restricted files on the server visible to an attacker.
Attackers use techniques such as special-character sequence and encoding of the sequence to bypass security filters and access restricted files.
Cybercriminals could also exploit directory traversal vulnerability in Trend Micro Worry-Free Business Security, which claims to offer cloud-based, enterprise-grade protection for your business devices and email, to make changes to critical files or download password files, among other things.
