Hackers have been caught fooling people into installing a Remote Access Tool (RAT) with the help of a fake NortonLifelock document. A remote access tool is generally used by hackers to gain unauthorized, remote access to their victim’s computer. And ironically, NortonLifelock is a cybersecurity company headquartered in the U.S. Meaning, hackers were clearly trying to impersonate a company, which essentially safeguards users against such activities.
It starts with a bogus NortonLifelock document
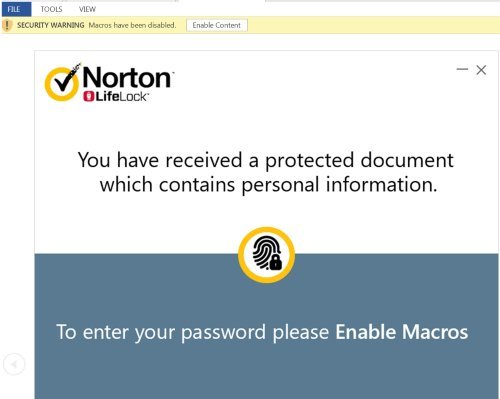
Hackers used a fake Norton Lifelock document in an attempt to install the payload onto their victim’s devices. It starts with a Word document disguised as a password-protected document from Norton Lifelock. In reality, it’s related to a phishing racket distributing NetSupport Manager. It’s nothing but a commercially available remote access tool (RAT).
Palo Alto Networks researchers find the use of a fictitious NortonLifelock document to fool users into enabling Macros. Here’s how it works!
According to researchers, the process begins when a victim opens a Microsoft Word document from within Microsoft Office Outlook. Researchers suspect that this activity could be a part of a much bigger phishing campaign since it also employs anti-detection techniques to evade dynamic and static analysis.
The bogus password-protected Word document appears to contain personal information of a victim. The macro is intelligently executed only after a victim opens the document and clicks “Enable Content.” It then prompts users to enter a password. Researchers also suspect that the password is provided in the phishing email and the dialog box accepts only the letters c in lower/upper case.
No malicious activity occurs until victims enter the correct password. As soon as victims enter the correct password, the macro continues to execute code and builds the command string, which ultimately installs NetSupport Manager RAT on the victim’s system.
“The macro obfuscates all strings using multiple labels on Visual Basic for Applications (VBA) forms, which contain two characters that are eventually linked together to construct the final command to download and execute the RAT on the victim.”
The payload installation leads to the addition of PowerShell script in the Windows %temp% folder, ultimately executing the RAT on the victim’s computer.
