CyberX announced that it had discovered a massive cyber-reconnaissance operation, Operation BugDrop that attackers were carrying out in a number of targets in Ukraine. This fairly recent attack eavesdrops on sensitive conversations by remotely controlling PC microphones – in order to surreptitiously bug its targets – and uses Dropbox to store exfiltrated data.
Operation BugDrop
CyberX believes that at least 70 targets, across different fields of practice including infrastructure, media and research, have been discovered and the number is expected to rise with time. The operation aims at capturing a wide variety of sensitive information from its targets including audio recordings of conversations, screenshots, documents, and passwords. The audio capturing works effectively because it cannot be blocked out manually as in the case of video recordings.
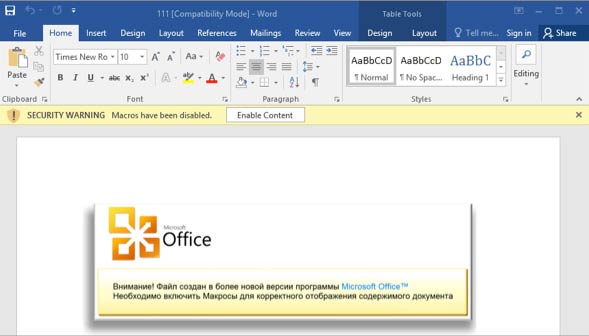
Malware remotely controlling PC microphones
The company also claims that Operation BugDrop is not just concentrated in Ukraine, and cases have also been reported in parts of Russia, in Saudi Arabia and Austria. Specifically, most of the targets are in the terrorist claimed areas of Ukraine. This kind of a well-planned operation requires a lot of investment and manpower, indicating that big organizations might be behind the attack. In particular, the operation requires a massive back-end infrastructure to store, decrypt and analyze several GB per day of unstructured data that is being captured from its targets. A large team of human analysts is also required to manually sort through captured data and process it manually and/or with Big Data-like analytics.
CyberX’s research team got to know about the operation by accident. Once discovered, the team reverse-engineered the code to find out its key elements (decoy documents used in phishing attacks, droppers, main module, microphone module), and other weak points. Despite that, CyberX currently has no evidence that any damage or harm has occurred from this operation, however identifying, locating and performing reconnaissance on targets is usually the first phase of operations with broader objectives.
This discovery raises a much larger question. Private and public sector organizations need to continuously monitor their IT and OT networks for anomalous activities in case their data is compromised. Organizations also need deep forensics to identify the scope and impact of a breach, as well as an enterprise-wide incident response plan that can be carried out quickly and at scale.
