Cybersecurity researcher Beau Bullock has shipped a new tool called MFASweep to help users check for Multi-factor Authentication (MFA) coverage on a Microsoft account.
Researchers believe inconsistencies in the way Microsoft has implemented MFA across different services such as Azure and Microsoft 365 and Azure secure some protocols as single-factor authentication.
MFASweep to verify if MFA is enabled across Microsoft 365
Due to endpoints being configured under different Conditional Access policy settings, the implementation of MFA is not consistent across different Microsoft services.
Organizations wanting to replace single-factor authentication often fail to ensure that MFA is enforced on all access portals. This is where the MFASweep tool will come in handy.
“To help both offensive operators and defenders check for MFA coverage on an account, I wrote a tool called MFASweep that attempts to log in to various Microsoft services using a provided set of credentials to identify if MFA is enabled,” Bullock said in his blog post.
What is MFASweep?
MFASweep is a PowerShell script. Some protocols end up being left single factor due to misconfiguration of conditional access policies and other multi-factor authentication settings.
Additionally, MFASweep can also check for ADFS configurations and can attempt to log in to the on-prem ADFS server if detected. Following is the list of Microsoft services compatible with MFASweep:
- Microsoft Graph API
- Azure Service Management API
- Microsoft 365 Exchange Web Services
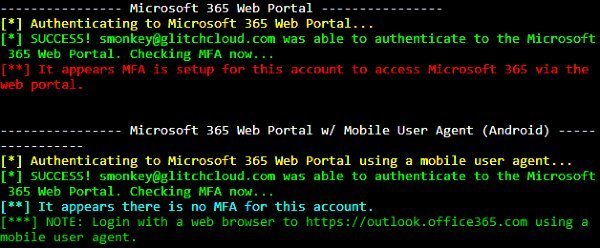
- Microsoft 365 Web Portal
- Microsoft 365 Web Portal Using a Mobile User Agent
- Microsoft 365 Active Sync
- ADFS
This MFASweep tool runs a command that requires the provided set of credentials to identify if MFA is enabled across these services.
Invoke-MFASweep -Username [email protected] -Password Winter2020
The following command not only runs with the default auth methods but also check for ADFS:
Invoke-MFASweep -Username [email protected] -Password Winter2020 -Recon -IncludeADFS
In related news, security researchers recently discovered critical vulnerabilities in Microsoft 365, allowing attackers to bypass multi-factor authentication (MFA).
These vulnerabilities could compromise user safety and privacy while interacting with cloud-based services. It could also allow attackers to gain complete access to their victim’s account data including emails, files, and contacts.
