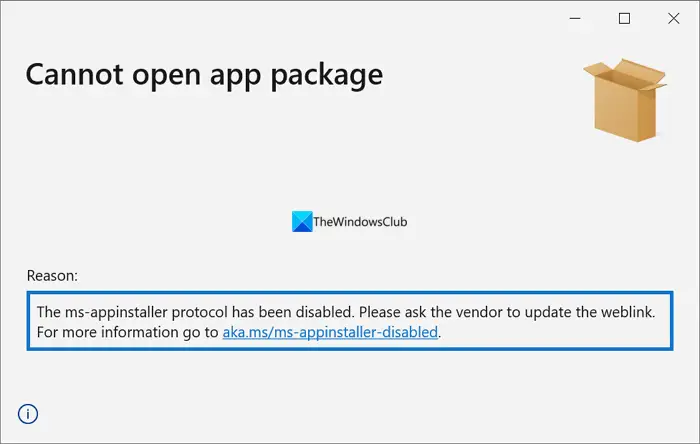
Microsoft Threat Intelligence has noticed that threat actors like Storm-0569, Storn-1113, Sangria Tempest, and Storm-1674 use the ms-appinstaller URI scheme (App Installer) to distribute malware. Microsoft has decided to disable the ms-appinstaller protocol handler by default to protect customers from malware and associated threats.
Microsoft disables ms-appinstaller protocol handler
Microsoft’s ms-appinstaller protocol handler is a trusted protocol that can bypass security mechanisms like Microsoft Defender SmartScreen and Edge’s built-in browser protection services. Threat actors have realized this and started using the ms-appinstaller protocol to distribute malware. Threat groups like Storm-0569, Storm-1113, Storm-1674, and Sangria Tempest started using the MSIX file format to distribute ransomware.
They register fake domain names that look as if they are official and trusted sources and upload installers for most used programs like Zoom, Tableau, TeamViewer, and Microsoft Teams. They have even spoofed the landing pages of OneDrive and SharePoint through Teams messages. The threat actors join one-to-one chats and meetings and lure the targets to install malware. Microsoft has noticed this since November 2023. As these malware and ransomware attacks are leading to financial loss to the targets/victims, Microsoft has disabled ms-appinstaller protocol handler by default.
The ms-appinstaller URI scheme handler is disabled by default in App installer build 1.21.3421.0. To reduce the impact of the threat, Microsoft has given some tips in its blog. They are:
- Pilot and deploy phishing-resistant authentication methods for users.
- Implement Conditional Access authentication strength to require phishing-resistant authentication for employees and external users for critical apps.
- Educate Microsoft Teams users to verify ‘External’ tagging on communication attempts from external entities, be cautious about what they share, and never share their account information or authorize sign-in requests over chat.
- Apply Microsoft’s security best practices for Microsoft Teams to safeguard Teams users.
- Educate users to review sign-in activity and mark suspicious sign-in attempts as “This wasn’t me”.
- Encourage users to use Microsoft Edge and other web browsers that support Microsoft Defender SmartScreen, which identifies and blocks malicious websites, including phishing sites, scam sites, and sites that contain exploits and host malware.
- Educate users to use the browser URL navigator to validate that upon clicking a link in search results they have arrived at an expected legitimate domain.
- Educate users to verify that the software that is being installed is expected to be published by a legitimate publisher.
- Configure Microsoft Defender for Office 365 to recheck links on click. Safe Links provides URL scanning and rewriting of inbound email messages in mail flow, and time-of-click verification of URLs and links in email messages, other Microsoft Office applications such as Teams, and other locations such as SharePoint Online. Safe Links scanning occurs in addition to the regular anti-spam and anti-malware protection in inbound email messages in Microsoft Exchange Online Protection (EOP). Safe Links scanning can help protect your organization from malicious links that are used in phishing and other attacks.
- Turn on attack surface reduction rules to prevent common attack techniques:
- Use advanced protection against ransomware
- Block executable files from running unless they meet a prevalence, age, or trusted list criterion
- Turn on PUA protection in block mode
Microsoft has advised companies who can’t immediately deploy the latest App Installer version to disable the protocol by setting the Group Policy EnableMSAppInstallerProtocol to Disabled.
