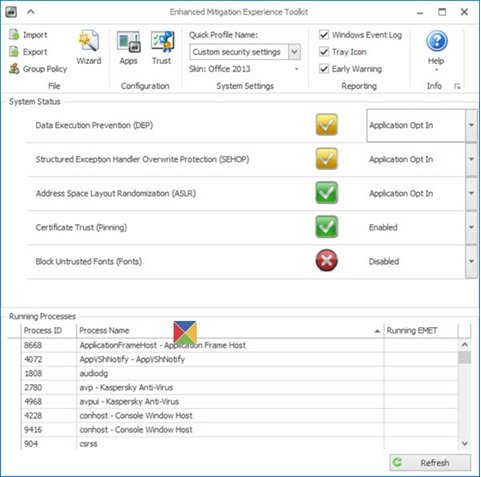
A recent report suggests vulnerabilities in Microsoft EMET tool can be exploited to disable all protections it enforces for other applications in Windows. Microsoft’s Enhanced Mitigation Experience Toolkit (EMET) is a free Windows-based security tool that adds an additional layer of security to defend Windows OS from potentially dangerous virus threats.
Researchers find Microsoft EMET exploit
EMET injects emet.dll or emet64.dll (depending upon the architecture) into every protected process, which installs Windows API hooks (exported functions by DLLs such as kernel32.dll, ntdll.dll, and kernelbase.dll). These hooks provide the tool ability to analyze any code calls in critical APIs and find if they are legitimate. If found to be legitimate, EMET hooking code jumps back into the requested API. If not, it triggers an exception.
Having said that, there exists a string of code within EMET that is responsible for unloading EMET. The code systematically makes EMET lose all of its protection capability and returns the program to its original i.e., unprotected state.
A person simply needs to find and call this function to completely disable EMET. In EMET.dll v5.2.0.1, this function is located at offset 0x65813. Switching to this function of EMET tool results in subsequent calls, which remove EMET’s installed hooks.
One simply needs to locate and call this function to completely disable EMET,” FireEye researchers reported in a blog post. “In EMET.dll v5.2.0.1, this function is located at offset 0x65813. Jumping to this function results in subsequent calls, which remove EMET’s installed hooks.”
What can be seen as of now is the exploit is a new attack vector that’s easier to employ than bypassing each of EMET’s individual protections as they were designed.
A few months back too another vulnerability was discussed that allowed attackers to bypass EMET with a single instruction. Like the earlier vulnerability, the current one too has been patched.
Since this technique is in public view, it is recommended that EMET users should upgrade to the recent version as soon as possible to avoid future attacks. In addition to Windows 10 compatibility, the recent EMET version improves the performance for the EAF and EAF+ mitigations.
