Recently Microsoft released important changes to detecting browser modifiers and adware, with a view to improving Internet Explorer security and browsing experience. Microsoft has mentioned the changes to how it detects browser modifiers and adware and they are:
- Unacceptable behaviors
- Browser consent dialogs
Unacceptable Behaviors:
Microsoft will detect the following browser modifier behavior:
- Bypassing dialog box that appears constantly asking user to install extension/addons/toolbar when they launch Internet Explorer
- Blocking a user from viewing or modifying browser features or settings.
Browser Consent Dialogs:
In most recent web browsers, browser consent dialogs have been disabled by default for all newly installed addons/toolbar/extensions. The Disabled by default model helps browser run securely, as those newly added extensions won’t load up with the browser, hence also improving privacy and security. These disabled addons won’t load until the next time the browser starts and asks for user permission to enable/disable them.
Developers are side-stepping these dialogs, using Group Policy settings, preferences file modification and registry changes to bypass it. For example they side-step your consent and install extensions, which is not an acceptable feature. These settings are meant o be used only by organization to deploy extensions. Side-stepping the consent, will result in the application being detected as a browser modifier.
UAC over Browser Settings and Features:
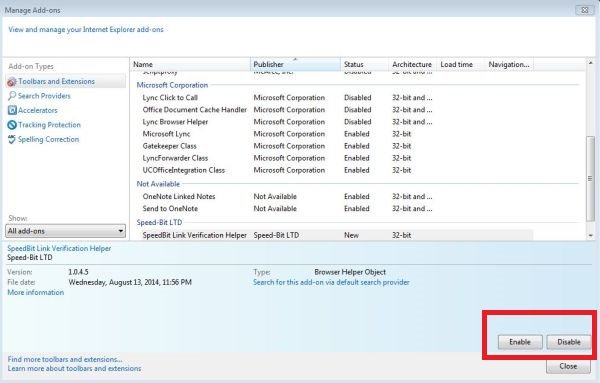
If an application does not allow users to disable addons which we may have enabled by mistake, even using Manage Addons, then such applications will be categorized as Adware or browser modifier by Microsoft security products, says Microsoft.