Microsoft has released a new version of Windows 10 Update Assistant to fix a local privilege escalation vulnerability, which blocks any attacker to use elevated privileges to run a program with System permissions. It would have lead to any action in Windows 10 by the attacker.
Windows 10 Update Assistant vulnerability fixed
Microsoft released the patch on Tuesday with security fixes, and details of this local privilege escalation vulnerability (CVE-2019-1378) in Windows 10 Update Assistant. Jimmy Bayne discovered it. The vulnerability was available in version 1903, which allowed an attacker to do anything with system privileges.
Microsoft Bulletin says:
An elevation of privilege vulnerability exists in Windows 10 Update Assistant in the way it handles permissions.
A locally authenticated attacker could run arbitrary code with elevated system privileges. After successfully exploiting the vulnerability, an attacker could then install programs; view, change, or delete data; or create new accounts with full user rights.
The security update addresses the vulnerability by ensuring the Windows 10 Update Assistant properly handles permissions.
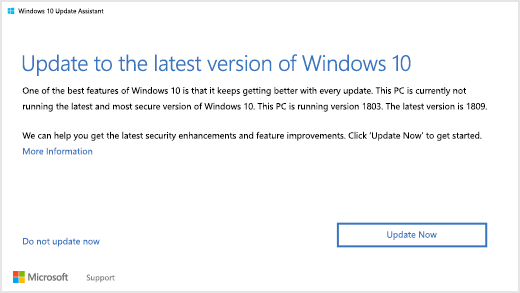
That said, the update should be available via the Windows update, or you can force uninstall the Windows 10 Update Assistant and download the latest version from by using the ISO.
To force uninstall, you need to run the following command in the elevated Command Prompt.
C:\Windows10Upgrade\Windows10UpgraderApp.exe /ForceUninstall
However, we suggest you update the Windows 10 Update assistant via Windows 10 Update method. Only if you feel something is wrong with your system, you may choose to force uninstall.
Microsoft in their bulletin page also says:
If in the past after being directed to the Download Windows 10 page you clicked Update Now and then SAVED the WindowsUpdate9252 installer executable file to your machine, you need to do the following:
- Delete the WindowsUpdate9252 installer file.
- On the Download Windows 10 page, click Update Now to get the updated installer, and follow the instructions to either Run or Save the installer.
We are glad that this has been fixed, and if you haven’t updated, you should do this as soon as possible.
