Evil Clippy, a tool designed by Dutch security researchers Outflank has been found to assist red teamers and security testers in creating malicious Microsoft Office documents. The tool, as reported, makes the malicious Office docs go unnoticed!
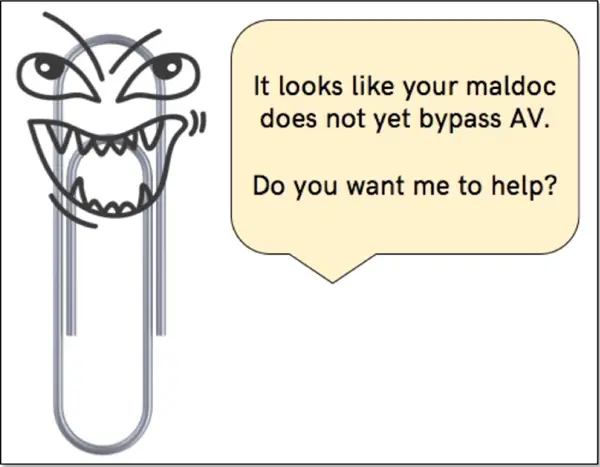
Evil Clippy can be considered as the demonized version of Microsoft Clippy (the animated paperclip that served as the virtual assistant for MS Office). It’s more like a pen-testing tool developed to help researchers find discrepancies against Office software.
Evil Clippy makes malicious Microsoft Office docs undetectable
The app relies on the technique of replacing the malicious VBA source code with a fake code whilst executing the malicious code via p-code. How does this happen? If the MS Office version specified in the _VBA_PROJECT stream matches the MS Office version of the host program (Word or Excel) then the VBA source code in the module stream gets overlooked and the p-code is executed instead. Any tool analyzing the VBA source code (such as antivirus) can thus be completely bypassed.
The most powerful technique of Evil Clippy is “VBA stomping”. VBA stomping abuses a feature which is not officially documented: the undocumented PerformanceCache part of each module stream contains compiled pseudo-code (p-code) for the VBA engine. If the MS Office version specified in the _VBA_PROJECT stream matches the MS Office version of the host program (Word or Excel) then the VBA source code in the module stream is ignored and the p-code is executed instead.
To test this claim, a user can replace the VBA source code in his malicious document with fake code and run the malicious p-code on 32-bit installs of Office 2016. You can run Evil Clippy with the following command line:
EvilClippy.exe -s fakecode.vba -t 2016x86 macrofile.doc
As seen, Evil Clippy can fool any tool capable of analyzing the VBA source code, including antivirus software. Also, it can hide VBA macros, stomp VBA code (via p-code) and confuse popular macro analysis tools. For more information, visit the Outflank webpage.
