Petya (or NotPetya) Ransomware (Or not ransomware) – it is the second major global Ransomware attack incident in the past two months. Petya, began in Ukraine and then it quickly spread further across Europe and the rest of the world. This Ransomware encrypts a hard drive’s index page until the victim pays the ransom of $300 in Bitcoins. Microsoft in a blog post shared the procedure to prevent and detect Petya through Azure Security Center for its customers.
Petya Ransomware Cyber Attack
Petya ransomware is very similar to the Wannacry attack, in fact, it follows the same pattern. The ransomware locks up a computer’s files and demands $300 Bitcoins as ransom to unlock the data. So far it has hit over 12,000 machines in around 65 countries. Once a system has been compromised, the ransomware takes the following steps:
- Pens a message to the raw disk partition.
- Clears the Windows Event log using Wevtutil
- Restarts the machine
- Encrypts files matching a list of file extensions (including .3ds, .7z, .accdb, .ai, .asp, .aspx, .avhd, .back, .bak, .c, .cfg, .conf, .cpp, .cs, .ctl, .dbf, .disk, .djvu, .doc, .docx, .dwg, .eml, .fdb, .gz, .h, .hdd, .kdbx, .mail, .mdb, .msg, .nrg, .ora, .ost, .ova, .ovf, .pdf, .php, .pmf .ppt, .pptx, .pst, .pvi, .py .pyc, .rar, .rtf, .sln, .sql, .tar, .vbox, .vbs, .vcb, .vdi, .vfd, .vmc, .vmdk, .vmsd, .vmx, .vsdx, .vsv, .work, .xls, .xlsx, .xvd, and .zip)
- Leverages WMI or PsExec to spread
- Presents a text message on the screen of the user, demanding ransom for files recovery.
Prevention Of Petya In Microsoft Azure Security Center
- Deploy Endpoint Protection
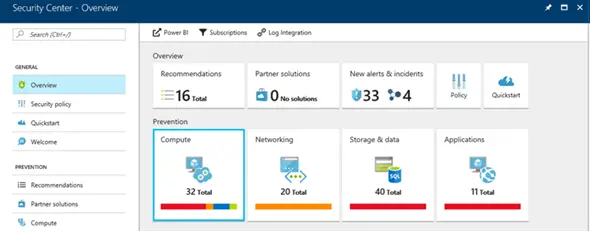
Azure Security Center runs a scan against the virtual machines across an Azure subscription. It then makes a recommendation to deploy endpoint protection where an existing solution is not detected, this can be accessed via Prevention section.
- Compute pane
The Compute pane displays the endpoint protection status in detail. This include recommendation for installing Endpoint Protection.
- Selection Of And Installation
Upon clicking on the recommendations on Compute Pane, the user leads to a dialog that allows the selection and installation of an endpoint protection solutions, including Microsoft’s own antimalware solution.
- Availability
Azure Security Center Free tier customers have access to these recommendations and connected mitigation steps.
Detection Of Petya In Microsoft Azure Security Center
- Detection Feature For Standard-Tier Azure Security Center
Standard-Tier Azure Security Center customers can reap the benefits of a recently added new detection feature. This feature specifically alerts on specific indicators related to the Petya ransomware running on an infected host. The security alerts can be accessed by the users through the Detection pane.
- Alert For Petya Ransomware
Alert for Petya ransomware displays as shown in the picture. To view the details of the impacted VM and suspicious process or commandline user needs to click on the alert.
Apply Remediation Steps To All
While the detection alert relates to a specific host, Microsoft advices to apply remediation steps to all on all hosts on the network. This is Petya attempt to spread to other nearby machines.
Microsoft Azure Security Center customers can follow the remediation steps from Microsoft Malware Protection Center (MMPC) blog.
