Researchers have discovered and analyzed a new crypto-ransomware variant with new routines, CrypVault, that encrypts files and make them appear as if they were quarantined files. The ransomware malware then deletes the key files using Microsoft Sysinternals SDelete tool.
The growing Ransomware menace is a result of existing cyber-criminal gangs realizing the revenue-generating power of the ransomware business model. The modus operandi is pretty straightforward – Encrypt something important and demand cash for its return!
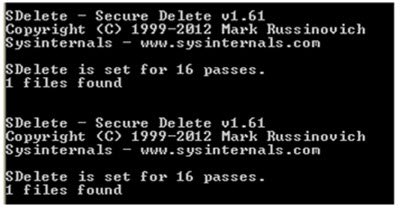
CrypVault Ransomware uses Microsoft Sysinternals SDelete
The files are appended by a *.VAULT file extension so as to make them appear quarantined by an AV solution. This helps in downloading info-stealer malware on machines infected and demand ransom for allowing access to files in return.
The ransomware variant arrives on target computers after tricking the users into downloading and running a malicious attachment – a Javascript file – that downloads four files: The ransomware itself, SDelete, GnuPG, and a GnuPG library file.
Upon launch, the malware successfully installs an open source encryption tool called GNU Private Guard (GnuPG) into the infected machine, which begins the encryption process. The files extensions it targets are of various formats. After encrypting the user’s files, the malware appends a *.vault file extension. Thereafter, each ‘locked’ and encrypted file displays a ransom note when opened.
“The malware deletes key files, secring.gpg, vaultkey.vlt and confclean.lst, by using sDelete, a Microsoft Sysinternals tool. sDelete is is capable of overwriting a deleted file’s disk data that makes it difficult or nearly impossible to recover deleted files,” says Marcos.
The malware uses some script to display the ransom note.
The infection also drops a .TXT file and displays a message on the infected desktop instructing users how to pay the ransom in return for decrypting the files. Since, the given ransom note and the ransomware support portal is in Russian, the campaign was initially started targetting Russian-speaking users.
In addition to the above, the ransomware downloads and executes Browser Password Dump, a hacking tool capable of extracting passwords stored by browsers which are then sent to the C&C server under control of the attackers, reports Trend Micro.
