With the rise in popularity of Android OS, the prevalence of Android malware too is growing rapidly. Roman Unuchek, a security expert at Kaspersky Labs proved this point when an Android application came to him and his team for analysis. The application file turned out to be a multi-functional Trojan.
Android Trojan
The newest malware scare named as as Backdoor.AndroidOS.Obad.a, infects the handsets of Android Smartphone users via a vulnerabilty existing in popular DEX2JAR (The tool is used by analysts to convert APK files into Java Archive (JAR) format)software. The vulnerability was spotted and exploited by the cybercriminals to disrupt the conversion of Dalvik bytecode into Java bytecode, eventually complicating the statistical analysis of the Trojan.
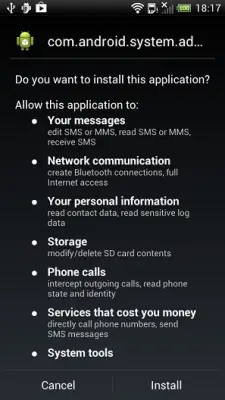
After this, the trojan procceds to install additional malware, distribute malicious software to other phones via Bluetooth, and perform remote commands in the Android console. Also, the cybercriminals noted an error in the Android operating system that relates to the processing of the AndroidManifest.xml file. This file exists in every Android application and is used to describe the application’s structure, define its launch parameters, etc.
Backdoor.AndroidOS.Obad.a alters AndroidManifest.xml in such a way that it does not comply with Google standards, but still correctly processed on a smartphone. All this working makes it extremely difficult to run dynamic analysis on this Trojan. Anyhow, this is nothing new as malware writers typically try to make the codes in their creations as complicated as possible.
To conclude this review, we would like to add that Backdoor.AndroidOS.Obad.a looks closer to Windows malware than to other Android trojans, in terms of its complexity and the number of unpublished vulnerabilities it exploits,” Unuchek wrote at Secure List.
Backdoor.AndroidOS.Obad.a does not have an interface and works in silent background mode.
