Microsoft has released a fix for critical Remote Code Execution vulnerability titled CVE-2019-0708. The vulnerability is pre-authenticated and requires zero human interaction. That being said the vulnerability can be exploited by a worm and any malware infected system can transfer it to another vulnerable computer.
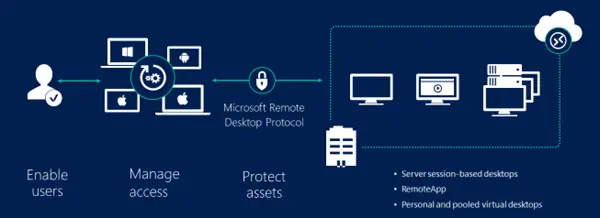
Remote Desktop Services, earlier known as Terminal Services in Windows Server, is one of the components of Windows OS that allow a user to take control of a remote computer or virtual machine over a network connection.
Prevent a worm by updating Remote Desktop Services
The propagation mechanism is somewhat similar to that of WannaCry malware. Currently, there is no exploitation of this vulnerability. However, it is quite possible that malicious actors will write an exploit for this vulnerability and embed it into their malware.
According to Microsoft, it is important that affected systems are patched as soon as possible. It is for this reason that Microsoft is offering a security update for all customers. Thankfully the update also supports select out-of-support versions of Windows. Vulnerable in-support systems include Windows 7, Windows Server 2008 R2, and Windows Server 2008. Out-of-support systems include Windows 2003 and Windows XP.
If you are using in-support versions the downloads can be found in here on Microsoft. The updates will get installed automatically if auto updates are turned on. On the brighter side, customers using Windows 8 and Windows 10 are not affected by this vulnerability. Microsoft says that it invests heavily in strengthening the security of its products and most of the times it is not possible to backport to earlier versions of Windows.
There is partial mitigation on affected systems that have Network Level Authentication (NLA) enabled. The affected systems are mitigated against ‘wormable’ malware or advanced malware threats that could exploit the vulnerability, as NLA requires authentication before the vulnerability can be triggered. However, affected systems are still vulnerable to Remote Code Execution (RCE) exploitation if the attacker has valid credentials that can be used to successfully authenticate. It is for these reasons that we strongly advise that all affected systems – irrespective of whether NLA is enabled or not – should be updated as soon as possible, says Microsoft.
The vulnerability exploited Network Level Authentication and the affected systems are mitigated against wormable malware and advanced malware threats. It is worth noting that affected systems are still vulnerable to Remote Code Execution (RCE) exploitation if the attacker has valid credentials that can be used to authenticate remotely.
The bottom line is that you need to update your systems as soon as possible. I personally feel that folks should move to Windows 10 since it offers superlative security features as compared to the earlier versions.
