Despite efforts to sniff it out, Spams continue to live. Microsoft Outlook supports some features that help to slow it down. Still, this menace continues to grow and expand its reach furthermore. The new Virobot ransomware-botnet is a case in point. A report published on TrendLabs says that Virobot, with both ransomware and botnet capabilities, is affecting users in the United States.
Virobot Ransomware with Powerful Botnet & Keylogging Capabilities
Its Botnet capabilities enable Virobot to quickly spread between computers via a spam e-mail attack vector using Microsoft Outlook as the transportation route. Once activated, Virobot-infected e-mails are instantly distributed to the Outlook contact list of the victim. The infected emails run a copy of the malware which if downloaded on the target machine infect it.
Once Viborot infects a system, it establishes itself as a part of a spam email botnet that distributes the ransomware to more victims. Surprisingly, Virobot was not found to be associated with any known ransomware families.
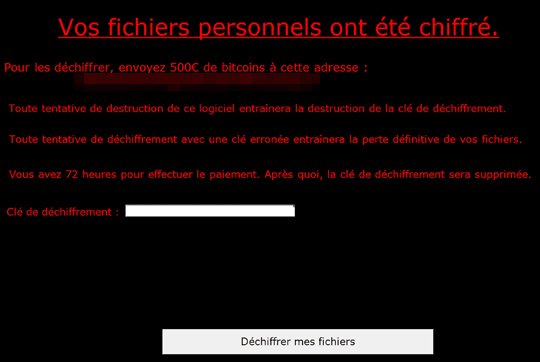
Virobot was first observed in the wild on September 17, 2018, seven days after we analyzed a ransomware variant that imitates the notorious Locky ransomware. Once Virobot is downloaded to a machine, it will check the presence of registry keys (machine GUID and product key) to determine if the system should be encrypted. The ransomware then generates an encryption and decryption key via a cryptographic Random Number Generator. Together with the generated key, Virobot will then send the machine-gathered data to its C&C server via POST, mentioned Trend Micro.
In addition to the above, Virobot features keylogger capabilities. This means it can record keystroke activity on an infected system and steal valuable personal information of the user. Besides, it can send these details to the C&C server.
As a precautionary measure, we can use smart technologies to eliminate spam emails before it reaches our network.
