This is the most innovative technique of breaching security that I have come across. You will surprised to know about this new vulnerability. Recently, two security researchers, during the demonstration last week at the CanSecWest conference in Vancouver showed how hacking a PC’s BIOS is an easy job.
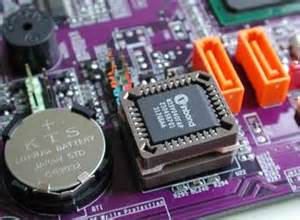
BIOS stands for Basic Input / Output System and is the first major software that loads on your computer system when it boots. It contains a set of rules or instructions that is needed in order to set up a communication between the operating system and the hardware.
Last week, the LegbaCore researchers showed how millions of computers contain vulnerabilities in their local BIOS chips, giving attackers a golden chance to perform malicious activities. Using this to their advantage, attackers can easily steal data and information from your system in a few minutes and can damage the system permanently.
SMM Incursion vulnerability in BIOS
While demonstrating the issue, researchers showed different vulnerabilities in SMM or System Management Mode. The role of the SMM mode of an Intel Processor is to allow the firmware to perform system functions. By gaining control of the SMM mode attackers can easily gain access to encrypted data including password as well.
Researchers Corey Kallenberg and Xeno Kovah explained how vulnerable the UEFI BIOS implementation carried out on the modern motherboards are. The US National Security Agency is more likely using the same techniques as suggested by these two researchers.
SMM malware gives attackers an ability to read all data that are present in the machine’s memory. Both researchers during the demo show how easily they were able to access the BIOS and then at the same time installed “Light Eater SMM payload”. “Light Eater SMM payload” is a malware that has the capability to extract GPG keys, passwords and steal decrypted messages from the Tails on an MSI computer where Tails is a privacy and security-oriented operating system.
How attackers can attack your system:
There are two ways which attackers can adopt to install the BIOS malware on your system. First one is through malware infection on your system either by an infected email or drive-by download and the second is when they physically get access to your computer.
How to prevent system from being attacked:
One of the best ways to protect your system and the data in it is by updating your BIOS to the latest version on the regular basis. Most of the people don’t install BIOS updates at all which give the attackers a chance to attack their system.
These LegbaCore Researchers have already reported several manufacturers about the issue who are now working towards a solution.
