Windows 10 users, beware. Emotet malware is on the loose yet again, Microsoft has warned. According to the company, a massive Emotet campaign has resurfaced affecting its users after being silent for months. However, it still employs the same old tactics. It all starts with emails carrying either malicious links or modified documents with malicious macros, which run a script that downloads malware payload from multiple URLs.

Emotet malware returns
“Emotet resurfaced in a massive campaign today after being quiet for several months. The new campaign sports longtime Emotet tactics: emails carrying links or documents w/ highly obfuscated malicious macros that run a PowerShell script to download the payload from 5 download links,” Microsoft tweeted.
Microsoft has already come across tens of thousands of emails and several hundreds of unique attachments and URLs involved in this massive malware campaign. However, Microsoft Defender Advanced Threat Protection (ATP) was able to detect this campaign, malicious attachments, and URLs in emails and block malicious components on endpoints.
What is Emotet malware?
First identified in 2014, Emotet is a banking trojan that has led some of the biggest and deadliest cybercrime threats in recent years. Earlier this week, there were signs of a potential comeback of Emotet malware after showing no signs of existence for months. In the past, Emotet has been used to spread Trickbot, Qakbot, and Ryuk ransomware.
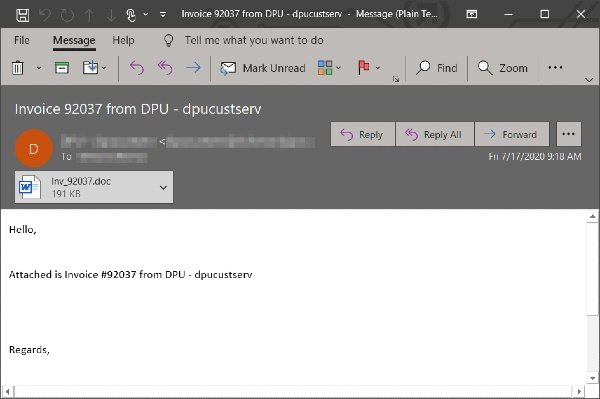
Emotet intrudes into your computers, courtesy of phishing email. Such emails consist of malicious attachments with these extensions .doc, .pdf, .xls, among others. The execution of these files leads to the execution of Emotet malware on your computer. In some instances, emails contain malicious links that download and launch Emotet.
Emotet malware can steal passwords and financial data, harvest email, spread spamming, lateral movement attacks, and other malware, among others. In fact, according to US-CERT, Emotet is one of the most costly and destructive malware that affects various governments across countries.
Earlier this year, security researchers discovered SMS-based Emotet malware infiltration, which uses the combination of SMS malware and phishing techniques also known as SMS Phishing or SMiShing. The aim was to gain unauthorized access to users’ online banking credentials and install Emotet malware.
