Microsoft has come to the rescue act once again as the company updates Windows Defender to periodically search and remove eDellRoot from the user’s PC’s. Dell has already been exposed with the potential threats that its self-signed root kit ( dubbed as eDellRoot ) could bring to Dell PC owners. The private key could expose users to attackers who can easily intercept HTTPs communication between the server and user’s PC loaded with eDellRoot. All this would mean that attackers could easily decrypt, modify or spoof HTTPS websites, including banking or social media, getting access to users’ private data.
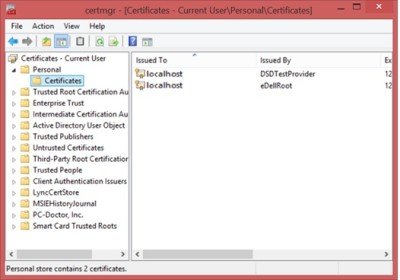
To make matters worse, just in a few days, Dell was detected 2nd time with another root kit known as DSDTestProvider, coming with a key again and lying in Dell’s support tools. The rootkits were installed by Dell Foundation Services application.
Windows Defender removes Dell’s DLL
While Dell released a fix to automatically remove eDellRoot from the PC, it was always an uncertain decision for its users to install it after such a breach of trust. However, with Microsoft, now updating Windows Defender to detect “Program:Win32/CompromisedCert.D” root certificate, users can easily remove Dell’s DLL from their PC.
Issuing an advisory note on Malware Protection Center, Microsoft said,
“If your Dell PC contains this certificate, it might be vulnerable to this threat. A PC with this certificate could be vulnerable to SSL/TLS spoofing attacks, and can allow an attacker to digitally sign binaries so that they are trusted by the affected PC. This can give an attacker control over your PC and browsing experience.”
PC’s with compromised certificate, may contain below Certificate Thumbprint hash
“CN=DSDTestProvider,HASH:02c2d931062d7b1dc2a5c7f5f0685064081fb221”
under the registry keys,
- HKLM\Software\Microsoft\SystemCertificates\ROOT\Certificates\
- HKCU\Software\Microsoft\SystemCertificates\Root\Certificates\
Dell PC’s with Windows 10, Windows 8, Windows 8.1 and Windows 7 are found to be affected with the rootkit certificates, said the company.