The latest Windows 10 operating system from Microsoft boasts of various security features to protect PCs from attacks. However, Security Researchers at CyberArk Labs have found a hole in the Windows Safe Mode that can be exploited by attackers to easily gain unauthorized access.
The Researchers have warned that an attacker with access to a compromised PC or server can easily make use of Windows diagnostic feature Safe Mode to get access to the victim’s PCs. Here is how the Safe Mode of your Windows PC can be exploited.
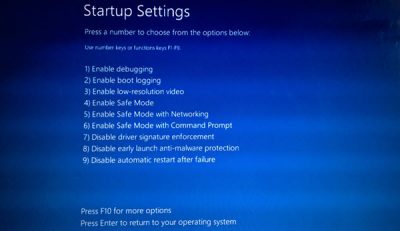
Windows Safe Mode is a long-standing, basic function of the Windows operating system that was designed by Microsoft to let users resolves PC’s related issues which users were unable to solve under Normal mode. As it has always been, only selected applications are allowed to run in Safe mode and even the 3rd party security tools and Antivirus programs are not allowed to run.
The attackers, as Researchers say, can exploit this Safe mode operation. They can remotely reboot PC’s into Safe Mode to disable and evade endpoint defenses and subsequently launch their attacks.
CyberArk mentions in its blog post,
“By exploiting these weaknesses, attackers can turn infected endpoints into launching points for pass-the-hash attacks, which can provide attackers with access to more machines on which they can re-use these same attack techniques to ultimately compromise the entire Windows environment”.
Using Safe Mode to escalate attacks
Safe Mode can be exploited to allow an attacker to capture user credentials and execute pass-the-hash attacks to achieve lateral movement. To do that, firstly attackers would look to change system settings to move the OS into Safe Mode during the next reboot. Next, prepare attack tools to load in Safe Mode and thereafter force the reboot of the machine to begin the exploit.
Although all Windows systems are vulnerable to Safe Mode attacks, users can take following steps to minimize the risks,
- Removing local administrator privileges from standard users so that attackers are not able to switch from Normal to Safe mode
- Rotate privileged account credentials so that even if the attackers able to capture the password hashes from compromised machines they would no longer be useful
- Use security tools that work in Safe Mode along with Normal Mode
- Continuously monitor any unusual activity that involves PC to operate in Safe mode
To read more on these attacks, read the CyberArk Labs blog post here.
