There’s news that a popular Windows Toolbox script used to add the Google Play Store to the Android Subsystem is infecting systems with malicious scripts. Apart from this, the script is also adding some unknown Chrome extensions and potentially other malware.
Windows Toolbox executes malicious commands
The incident came to light when a handful of users discovered, that the Toolbox script downloaded from the GitHub page performed all the functions as given in the description, but hid something sinister. It got multiple scripts from Cloudflare workers and exploited them to execute malicious commands or download files to the infected device.
For instance, to run Windows Toolbox successfully, the developer requested users to run a command that resulted in loading a PowerShell script from a Cloudflare worker hosted at http: //ps.microsoft-toolbox.workers.dev/.
It’s quite a task to pick malicious scripts using Cloudflare workers as cybercriminals can modify the scripts as needed. Only last year during the October month, when the Windows 11 release was announced, Microsoft had declared that it would allow users to run native Android apps directly from within Windows.
However, when the Android for Windows 11 preview was released in February, many were left disappointed as they could not use it with Google Play. As such, they were left stranded with apps from the Amazon App Store.
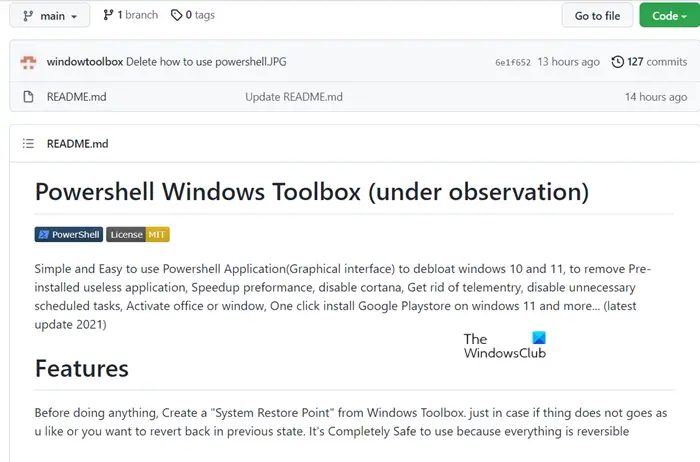
Around the same time, some unknown developer released a new tool called Windows Toolbox on GitHub with a host of features. Among other things, it supported Google Play Store installation for the Android subsystem on Windows.
Sadly, the tool that was hailed as a wonderful alternative turned out to be a Trojan that cleverly executed a series of malicious PowerShell scripts to install a trojan clicker and possibly other variants of malware on devices.
Via BleepingComputer.
