Potentially Unwanted Programs (PUPs) tend to interfere with everyday computer use by placing advertisements, tool-bars in web browsers and resorting to other nefarious tactics. Options that generally trick you into installing potentially unwanted programs are common during the setup of free tools and programs. WinYahoo is one such program that borrows tricks from malware authors to inject malware in your system.
WinYahoo PUP hijacks browser preferences
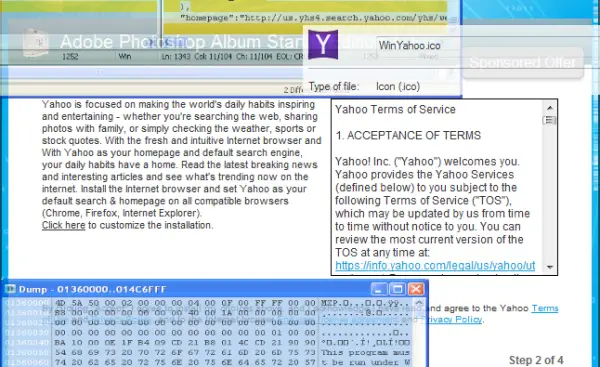
It requires expert skills and experience to identify all the files of WinYahoo infection. Like a lot of unwanted software, WinYahoo comes bundled in with a parent installer (md5: 41e092385fb06a3087cd0027375e2288). The mentioned file is a bundler for Adobe Photoshop Album Starter Edition. The bundler allows the software to modify Google Chrome’s secure preferences without being detected by the browser.
Secure preferences in Chrome are located in a file called “Secure Preferences”. In the Secure Preferences file, there resides a section called “protection” where various user preferences are stored along with a generated hash value known as a Message Authentication Code (MAC).
The MAC is used to protect the integrity of the data and therefore any changes made to it raises red flags. These MAC values are checked when the browser loads along with another MAC called the “super_mac”. WinYahoo PUP makes these changes successfully by calculating new MACs, thus hijacking the user preferences.
An article on Malwarebytes blog highlights in detail deceptive techniques that WinYahoo PUP uses to deliver advertised software to the users. The blog mentions, WinYahoo also installs a rogue Chrome extension that injects JavaScript into webpages. During the tests conducted by MalwareBytes team, the extension called “Sale Charger,” was installed which was identified when looking at the installed extensions list.
The extension exhibits the rather annoying feature of creating new tabs in web browsers with advertisements. In one case, a Tech Support Scam was presented, a topic discussed in the earlier past by us.
