IT security professionals try building high-performance security tools keeping in view the changing nature of the threat landscape. However, they note two fundamental issues have stayed constant. First, the threat landscape continuously evolves and gains sophistication. Second, attackers remain a step ahead of the defenders in exploiting vulnerabilities across developing technologies.
Threat Landscape in European Union is changing
Microsoft Director of Security Tim Rains had a chance to visit Europe and notice the change in the threat landscape. In his blog post, he provides a closer look at the threat landscape in the European Union where malware and ransomware encounter rates are on the rise.
“It would be easy to believe that the threat landscape just got a whole lot worse, but that’s not really the case. Every month, the Microsoft Malware Protection Center typically adds detection capabilities to the MSRT (Malicious Software Removal Tool) for one or more new families of malware that researchers believe are globally prevalent. Then the MSRT executes on 600 to 700 million systems worldwide. If researchers were correct about the families they added to the MSRT, the MSRT will clean the newly added threats from systems infected with those threats around the world”, writes Rain.
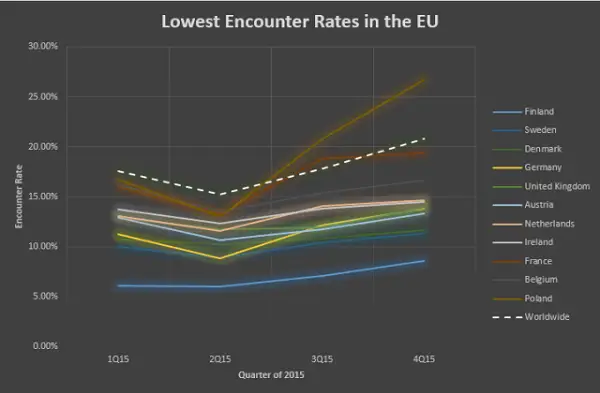
It is observed that in the EU, 18 of 28 countries had ransomware encounter rates above the worldwide average. ER represents the percentage of computers running Microsoft real-time security software that report detecting malware or unwanted software during a given period of time.
Findings reveal, that the locations with the highest ERs in the EU include Romania (31.3%), Bulgaria (29.8%), and Croatia (27.5%). Moreover, systems in Portugal and Italy encountered ransom-ware more than any other locations in the EU. The upward trend in the ER seems more pronounced when these systems encounter malware and are tested successfully for malware infection, a measure called computers cleaned per mile (CCM).
Based on the specific threats noticed, the blog post offers some words o wisdom to help protect a user his organization like regularly checking for security Updates. Since, it’s critical for organizations to keep all software up to date with the latest security updates and keep the Anti-Malware Software up to date.
For more, visit here.
