Information, unknowingly leaked from people’s devices is a major reason to worry. The activity not only exposes them to a barrage of attacks or threats but can also encrypt their data, asking for money in exchange to unlock the same. Locky ransomware was one of such potential threats of the past year.
The ransomware was built and distributed by tech-savvy criminals as Ransomware as a Service (RaaS) offerings. There were other threats as well. Understanding their evolutions will play a key role in for building a strong defense. Cisco Annual Cybersecurity Report (ACR) creates a visualization scheme to summarizes these threats. Incidentally, if you do not know, Cisco completed its acquisition of OpenDNS and OpenDNS is now called Cisco Umbrella.
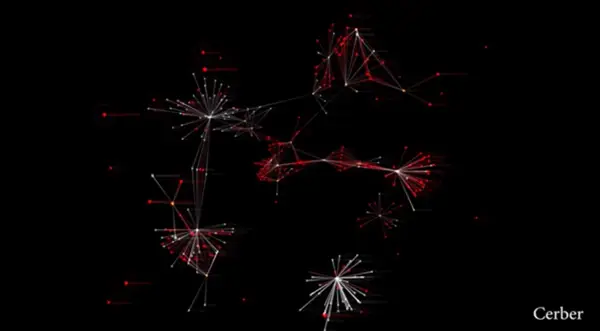
Visualization of 2016’s Top Threats
In this scheme, researchers selected a number of domains, labeled or tagged as the particular threat, then used the Investigate API to pivot across co-occurring domains, IP addresses, file hashes, registrant information and other attributes to build a graph of their relationships. Finally, the team used OpenGraphiti to visualize these graphs and reveal its structure. The result can be seen in the video below.
- Red node flags blacklisted domains
- Gray nodes – benign domains
- Green nodes – signals domain is safe for use, popularly known good domains
- Orange – indicates IP addresses
- Blue nodes – Notify file hashes.
The pulses in the network indicate DNS traffic between nodes.
This visualization represents Locky Ransomware, and as seen, it was one of the potential threats of the past year. The cluster of red nodes at the tip of the key shows the tightly interconnected structure of the domains used to host malware and generate keys.
Another Ransomware used as a popular exploit kit was ‘Cerber’. Visualizing its domain structure helped in revealing the threat’s infrastructure and how it’s used to host ‘Cerber’ and other malware. These threats along with many others (Nemucod, Dridex, GozNym/Kryptik) targeted mainly Windows OS as it remains the primary target of most malware. Main reason that can be attributed to this development – market share of the OS.
You can take a look at all the visualizations on their blog.