Recently, a vulnerability was discovered in the SSL 3.0 protocol, referred to as the Poodle Attack, which allows hackers and attackers to inject malicious code into your computer or web hosting servers. We have already covered in that post, how you can manually disable the use of SSL 3.0 by Internet Explorer, Firefox and Chrome browsers.
Disable SSL 3.0 in Internet Explorer
This is an industry-wide vulnerability affecting the SSL 3.0 protocol and is not specific to the Windows operating system. To be successful, the attacker needs to make several hundred HTTPS requests.
Says Microsoft:
In a man-in-the-middle (MiTM) attack, an attacker could downgrade an encrypted TLS session forcing clients to use SSL 3.0 and then force the browser to execute malicious code. This code sends several requests to a target HTTPS website, where cookies are sent automatically if a previous authenticated session exists. This is a required condition in order to exploit this vulnerability. The attacker could then intercept this HTTPS traffic, and by exploiting a weakness in the CBC block cipher in SSL 3.0, could decrypt portions of the encrypted traffic (e.g. authentication cookies).
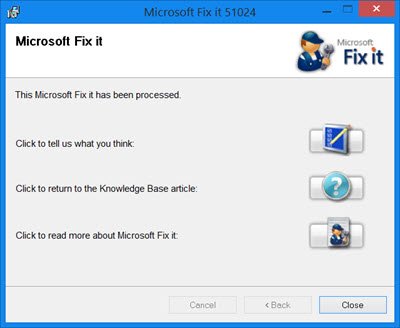
Seeing the seriousness of the problem and the potential for major damage, Microsoft has quickly released a Fix It that lets users disable SSL 3.0 in Internet Explorer. This Fix It is meant to be a workaround and not intended to replace any security update.
The Fix It is supported on Windows Server 2012 R2, Windows 8.1, Windows RT 8.1, Windows Server 2012, Windows 8, Windows RT, Windows Server 2008 R2 SP1, Windows Web Server 2008 R2, Windows 7 SP1, Windows Server 2008 SP2, Windows Vista SP2 and Windows Server 2003 SP2.
Microsoft has also announced that SSL 3.0 will be disabled in the default configuration of Internet Explorer and across Microsoft online services over the coming months, and recommends that customers migrate clients and services to more secure security protocols, such as TLS 1.0, TLS 1.1 or TLS 1.2.
Download links:
- Microsoft Fix it 51024 will disable SSL 3.0 in Internet Explorer
- Microsoft Fix it 51025 will restore the original settings of SSL 3.0 in Internet Explorer.
Once you have downloaded the Fix It, simply run it and let it do its work.