The programs used to create malicious documents that exploit vulnerabilities in Office applications such as Word are now being advertised in underground forums. One such new tool that has recently come up offers the ability to track the effectiveness of campaigns. Microsoft Word Intruder (MWI)as the program is known, is advertised as an “APT” tool to be used in targeted attacks.
Microsoft Word Intruder
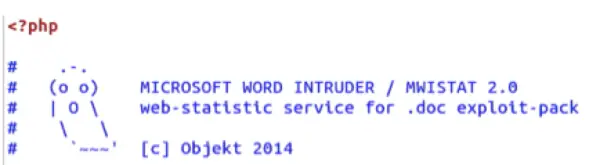
Reports suggests Microsoft Word Intruder, is likely developed somewhere in Russia and accompanied by a statistics package known as “MWISTAT” that allows operators to track various campaigns. It is advertised on the underground by an individual who goes by the handle Objekt.
How does the program work? Microsoft Word Intruder generates Rich Text Format (RTF) documents that are booby-trapped to exploit vulnerabilities in Microsoft Word. The most recent version of the program is capable of delivering multiple vulnerabilities in the same document, piled up one after another.
FireEye reports, samples of MWI produced since December 2014 include a special tracking feature called MWISTAT, which embeds a distinctive URL in the generated RTFs. It’s particularly noteworthy to mention here that malware delivered in booby-trapped Office files tends to fall into two categories:
Droppers
This includes one or more encoded malware programs (EXE files) as data that are unscrambled and written directly to disk during the infection process. This means that once you have received the booby-trapped file via medium such as an email or other message, you already have all components of the final malware available locally and the infection can infiltrate even if you are offline.
Downloaders
It contains a URL from which the final infectious malware payload is downloaded and installed, leaving you clueless about exactly what malware the booby-trapped files might deliver. The case is so because, the attackers can vary the download at will.
Much like Browser Exploit Kits, this tool Microsoft Word Intruder, lets even the minimal technically qualified, access Document Exploit kits, by allowing them to purchase them.
