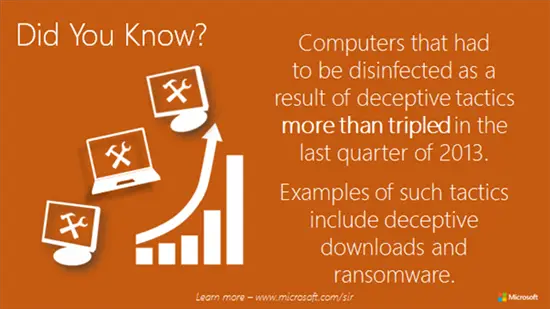
New elementary data released by Microsoft signals an increase in deceptive tactics employed by cybercriminals in attacking software making it both, difficult and expensive to get rid of such potential annoyances in quick time. The data in brief outlines key findings of Microsoft’s latest cybersecurity report brought out twice every.
Microsoft Cybersecurity Report
The report is intended to help customers, partners, and cybersecurity community at large by making them aware and giving knowledge of the tools, tactics and threats posed by cybercriminals. The company believes, knowledge is essential for IT and security professionals trying to better protect themselves and their organizations from cyber-attacks.
The report adds that one of the most common tactics used by cyberpunks to target users was deceptive downloads, where victims are drawn into the lure of downloading some music or video online, but end with downloading only a bundle of malware.
The second method dominates discussion these days – Ransomware. The software often pretends to be an official-looking warning from a well-known law enforcement agency accusing its victim of committing a computer-related crime and demands a pay as fine to regain control of the computer, a popular deceptive practice in vogue.
Tim Rains, director of Trustworthy Computing at Microsoft, said: “Keeping cybercriminals on the run requires a robust security strategy, the safest houses don’t just have locked doors, they have well-lit entry points and advanced security systems. It’s the same with computer security – the more we layer our defenses the better we are at thwarting attacks.
Words of wisdom from Microsoft to avoid such unwanted dangers,
- Download Software from trusted download sources only
- Keep all software or programs up-to-date.
- Back up files and run antivirus program every time you download a program.
Besides, migrating to Windows 8.1 gives users a chance to prevent their systems from being attacked by malicious software and modernize it at the same time. Research conducted by Trustworthy Computing’s Security Science team showed a 70 percent decline in the number of severe vulnerabilities (those that can enable remote code execution) that were exploited in Microsoft products between 2010 and 2013.