There is a malicious stalkerware app on the loose that tracks all of your social media activities. If you are an Android user, you need to be extra careful about apps that you install on your phone. Because no matter what, you don’t want a stalkerware app like the one researchers have just uncovered installed on your device, do you?
Researchers at Kaspersky have uncovered a new stalkerware app called MontorMinor, which can track your Gmail, WhatsApp, Facebook, and Instagram activities. Going by the brief description of this stalkerware, obviously, the creators of this app have bad intentions.
MonitorMinor stalkerware can intercept SMS & call data
In a nutshell, as researchers also explain, the basic idea behind stalkerware apps is to keep a track of the victim’s geolocation coordinates. However, modern stalkerware apps have become more advanced. They can also intercept the victim’s SMS and call data.
As data has become cheaper, SMS conversations have lost their significance in the last few years. These days, SMS are used primarily for receiving one-time passwords (OTP), nothing else. Meanwhile, social media and instant messaging apps like WhatsApp, Facebook, and Instagram have flourished to a great extent.
As a result, hackers have shifted their focus more towards these apps. But in Android, direct communication between apps is prevented by an access model called Discretionary Access Control (DAC):
“When an app is installed in the system, a new account and app directory are created, the latter being accessible only to this account. For example, WhatsApp stores the user’s chat history in the file /data/data/com.whatsapp/databases/msgstore.db, which only the user and WhatsApp itself have access to. Other messengers work in a similar way.”
MonitorMinor counts on the special root privileges obtained by a SuperUser-type app (SU Utility). When the SU Utility is installed on the device either by a user or a malware, the stalkerware app gains full access to the app data including your private conversations. Following is the list of apps that remain vulnerable to MonitorMinor infections:
- LINE: Free Calls & Messages
- Gmail
- Zalo – Video Call
- Kik
- Hangouts
- Viber
- Hike News & Content
- Skype
- Snapchat
- JusTalk
- BOTIM
In addition to intercepting data from social networking and messaging apps, MonitorMinor can also extract the file /data/system/gesture.key from the device, further compromising your device’s screen unlock pattern or the password.
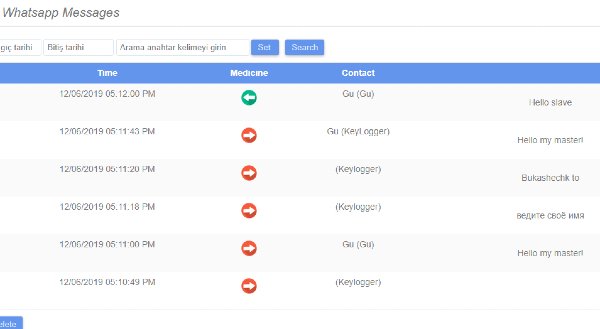
The Accessibility Services API allows the device to read aloud incoming messages and any other text in app windows. MonitorMinor uses this API to intercept private conversations from the above-listed apps.
The stalkerware enables hackers to control the device using SMS commands, view real-time video from the device’s cameras, record sound from the device’s microphone, view browsing history in Chrome, and View the contacts list, among others.
Researchers reveal that India is largely affected by the MonitorMinor stalkerware with 14.71% installations, followed by Mexico (11.76%), Germany, Saudi Arabia, and the UK (5.88%).
Leave a Reply