VPNs or Virtual Private Networks are trusted these days to keep user’s internet connection safe and private and find extensive use both at the individual as well as enterprise level. However, a recent report by Researchers has shown that at least 4 of the top 20 popular VPNs were highly vulnerable to malware.
A statement issued by industry research firm VPNpro says that crucial vulnerabilities in PrivateVPN and Betternet can allow hackers to push fake updates and install malicious programs or steal user data.
4 of the top 20 popular VPNs were highly vulnerable to malware
Researchers at VPNpro analyzed 20 different VPN software and discovered devastating flaws in Betternet and PrivateVPN in particular. Acting as white hat hackers, VPNPro rigged up a fake update and tried to hijack the installation process for multiple VPN programs. The research firm was successful in breaking through Betternet and PrivateVPN defenses and tricked programs into downloading the bogus update.
Terming the vulnerability as “Serious”, VPNpro said,
This is a serious problem: with the ability to push users to install fake updates, the hacker can install any program on a user’s computer or do a variety of malicious things.
Exploiting the vulnerability, hackers can,
- Steal personal data and sell it on the black market
- Make bank payments using the victim’s PC
- Secretly mine Cryptos
- Add the device to a botnet
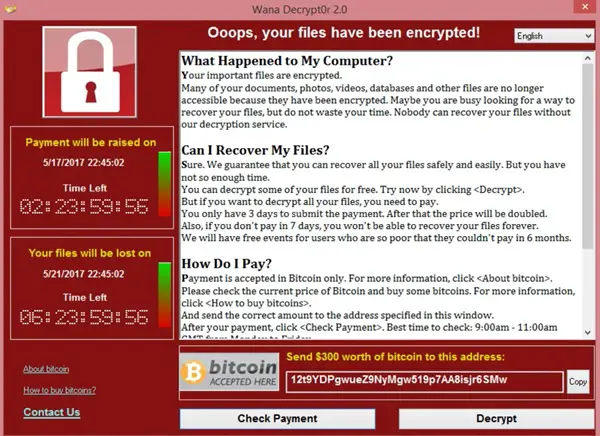
- Lock the PC demanding ransomware
- Steal the victim’s pictures, videos, recordings, and messages
How VPNPro intercepted the connection
VPNPro said that it was possible to intercept the communications between the VPN program and the app’s backend infrastructure. PrivateVPN downloaded VPNPro fake update and automatically executed it without needing the user’s approval. While on the other hand, Betternet downloaded the fake update but did not automatically execute the update and instead, popped a notification for the user to update the app (which most users will do at one point or another).
VPNPro also tested, Torguard and CyberGhost, and both allowed for interception of communications and connected while being intercepted.
Hotspot Shield and Hide Me also allowed for easy interception of communications but did not connect while being intercepted.
Vulnerabilities work only on Public Wi-Fi
According to VPNPro,
In order for hackers to carry out the attack, they’ll need one of two things. In the first option, the hacker would need to be on the same network as yours. Usually, the hacker can do this by duping you into connecting to a fake wifi hotspot (such as “Cofeeshop”) rather than the shop’s real wifi (“Coffeeshop”).
Alternatively, the hacker would have to have access to your router, and then you should be using the DNS server from the router’s DHCP service.
Betternet and PrivateVPN issue updates
VPNPro though verified that Betternet and PrivateVPN were able to present a patch. Both even sent a version to test. PrivateVPN rolled out the patch on March 26 while Betternet released their patched version on April 14.
How to stay protected
To stay protected, it is strongly advised against downloading anything, including updates, on free public WiFi. Also, ensure that you have an effective antivirus program that can help in stopping the malicious updates.
